Kiosk: an Easy Windows kiosk escape from secdojo
Overview
A Windows kiosk escape challenge. The machine runs in kiosk mode with a restricted browser-based interface. The objective is to break out of the kiosk environment and escalate to administrator.
Reconnaissance
Note: This writeup moves quickly through reconnaissance. For a detailed breakdown of the recon methodology, see the Cascade writeup.
though the tags of this machine say it’s an AD machine, it’s not actually, we run a pretty basic nmap -A on the target 10.8.0.2 :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
< SNIP >
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds?
3389/tcp open ms-wbt-server Microsoft Terminal Service
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
5986/tcp open ssl/wsmans?
| ssl-cert: Subject: commonName=INFO-PC
| Subject Alternative Name: DNS:INFO-PC, DNS:INFO-PC
| Issuer: commonName=INFO-PC
| Public Key type: rsa
| Public Key bits: 4096
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-06-22T16:16:36
| Not valid after: 2028-06-21T16:16:36
| MD5: f68e 2590 3444 9169 af1f c381 1706 bcda
| SHA-1: 6e8c 39ec d5fc 921d b4f2 a6cd d72b b7f0 3ce0 b196
|_SHA-256: 8e7c e9d2 e4b2 7659 b50b 2022 02fd f70b e411 a15b e642 7b77 a283 f6de 266e 109d
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
< SNIP>
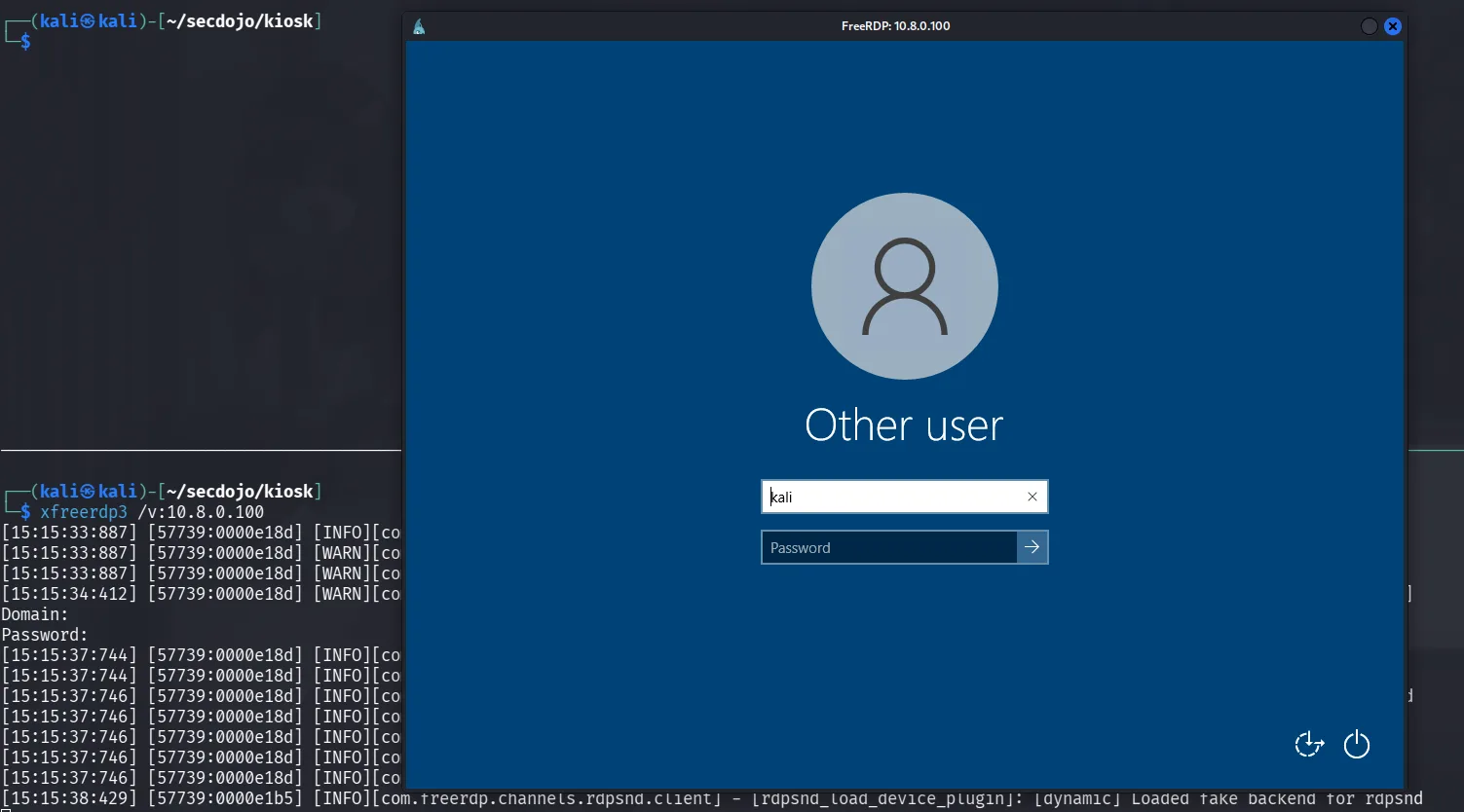
the name of the machine itself is a hint that we’re dealing with a kiosk, we can try rdp to it using xfreerdp:
we need valid credentials which we don’t have yet, we can attempt loging with Guest account but it didnt’ work, but we know this is windows running in kiosk mode, and acording to this article https://www.velessoftware.com/set-up-windows-kiosk-mode/ the default account that is created by default is kioskUser0, so we can try loggin with it with empty password.
Exploitation :
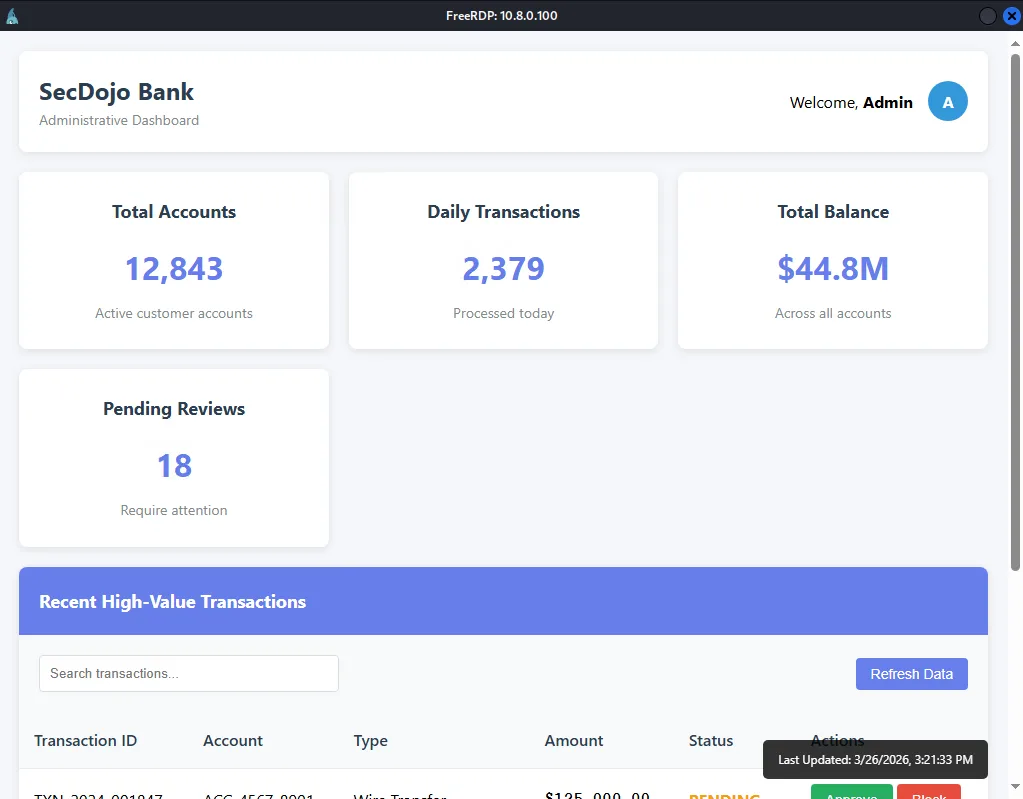
login with kioskuser0 and empty password works and we get redirected here, this seems to be some banking system:
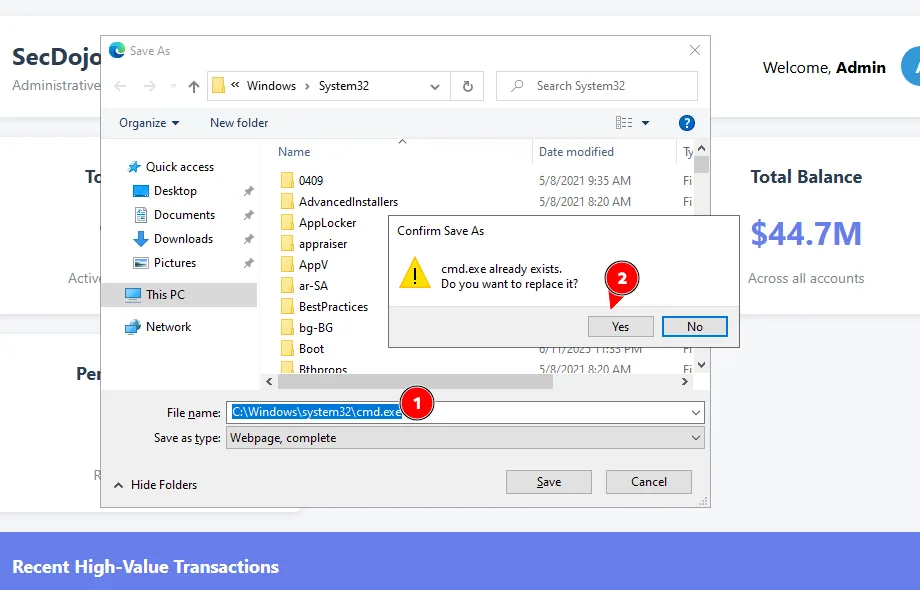
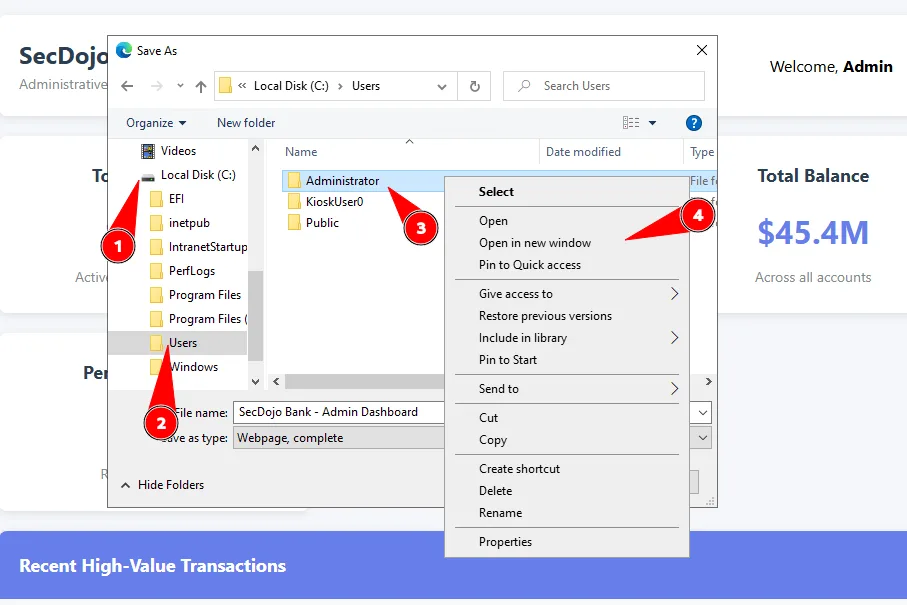
from here we should look for ways to escape the kiosk mode and find a way to execute commands, open up powershell or cmd.exe etc. there are many ways to trigger this, one of them is if we attempt to save the current page we’re seeing, as an html, we can hit : Ctrl+s => this will save the page as html, and in doing so it will open a windows asking us where to save the file, that’s our escape vector, we can go for using the right click and open a file in a new windows and look for powershell.exe or cmd.exe and start them etc .. this isn’t something I’m proud of but I kinda overcomplicated this in my first attempt, I thought the kioskUser0 is just a normal user and can’t read the flag, but once you get a cmd.exe it’s actually over as he’s in the administrators group, wished if there was a privilege escalation vector once we escape the kiosk mode, in my first attempt I escaped the kiosk mode, found a way to priv esc using this :
1
icacls C:\IntranetStartup\OpenIntranet.ps1
this shows that this file can be modified by us as we had FullControl over it and it runs as SYSTEM, and to trigger it we just need to log off and relogin again, we can modify it using notepad.exe :
1
notepad.exe C:\IntranetStartup\OpenIntranet.ps1
we simply add a line at the buttom to add a new administrator user, which we can use to read the flag, but as I said I have no idea why I didn’t check if the KioskUser0 is in the administrators group, or maybe I did and something changed in the lab now, it’s been long since I solved it, and I really that was the intended way, well there is some sense to it, thta I wouldn’t check, thought KioskUser0 wouldn’t be a privileged user since a service is running in its context but it is what it is.
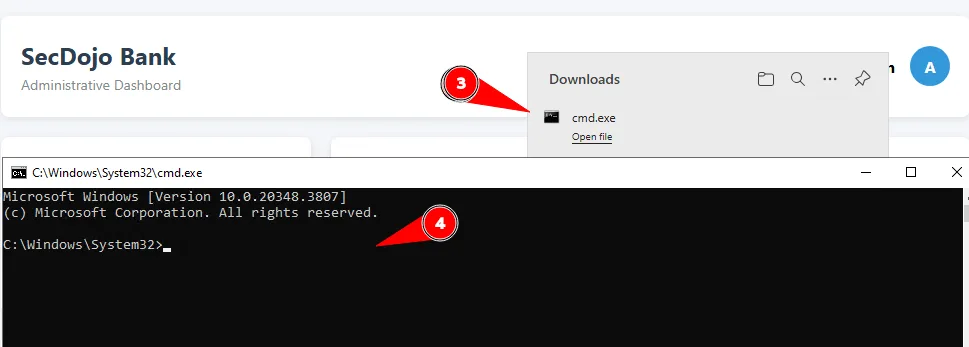
this another way below in the images below, we just resave cmd.exe itself in the path C:\Windows\System32\cmd.exe
and now it shows here we can open it:
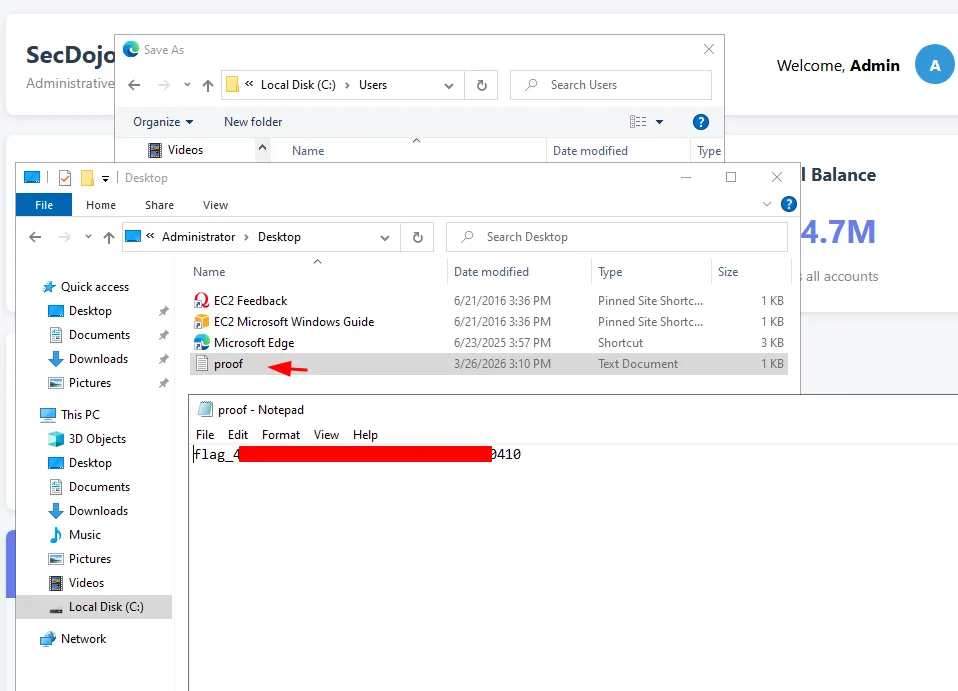
or we can go for the flag directly and not save anything, the flag would be in the Administrator Desktop, we just go for it as in the images here :
and:
1
2
PS > C:\Users\Administrator\Desktop>type proof.txt
kiosk_v1_dedicated_40642-3ny2a6iwrdouysvbfx8e8j29dwdx5av8
A kiosk escape challenge is a niche but well-executed scenario.